Radiflow, a maker of Industrial Control System (ICS) network security solutions, has introduced a new Intrusion Detection System (IDS) designed specifically for Operational Technology (OT) networks.
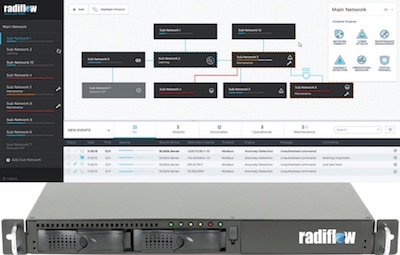
The new product, Radiflow iSID, enhances visibility and control in OT and was developed to simplify the network security workflow, so that operators don’t need to be network security experts, the company explained.
 Although isolated from the Internet, in recent years several vulnerabilities have been detected in ICS/SCADA networks due to changes in infrastructure companies’ (electric and water utilities, oil and gas) operational processes, Radiflow said.
Although isolated from the Internet, in recent years several vulnerabilities have been detected in ICS/SCADA networks due to changes in infrastructure companies’ (electric and water utilities, oil and gas) operational processes, Radiflow said.
“The threat to ICS networks is posed by motivated groups such as governments and elite hackers–all while the attack surface is high, and operators’ capabilities to effectively detect and react to ICS cyber incident are low,” noted Yehonatan Kfir, CTO, Radiflow. “This gap, between attacker and defender, poses a significant risk to the ICS process.”
Radiflow’s SCADA IDS is server-based software that analyzes OT network traffic and can be deployed both at the control center and at remote sites without any network intervention, the company said.
iSID combines SCADA/ICS modeling and Anomaly detection and receives a parallel (mirrored) stream of all network traffic which it analyzes to generate and display a network topology model, and serve as a baseline for detecting exceptions indicating unauthorized traffic.
The solution leverages six detection engines to specific network vulnerabilities such as changes in the network topology, validation of policies for maintenance tasks and for M2M sessions using DPI, signatures for known malware and sensitive SCADA commands, model-based anomaly detection for the SCADA process and for the characteristics of the traffic flows.
“Many of our U.S. customers have brought up the same two issues: managing maintenance processes and mapping the network traffic within their substations,” said Ayal Vogel, VP Business Development, Radiflow.
Related: Learn More at the SecurityWeek ICS Cyber Secrurity Conference
















