Cloud company Rackspace has confirmed being targeted in a ransomware attack after it was forced to shut down its Hosted Exchange environment.
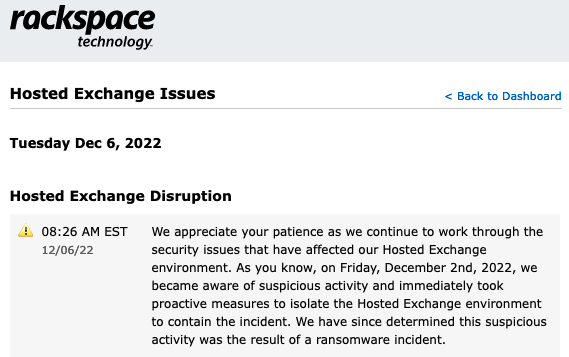
Rackspace’s hosted Microsoft Exchange service started experiencing problems on Friday, December 2. The company shut down the impacted environment and confirmed on Saturday that it was a security incident.
On Tuesday morning, the company confirmed that the suspicious activity causing the disruption was the result of a ransomware attack.
SecurityWeek has checked the leak websites of several major ransomware groups, but has not seen any mention of Rackspace. However, since the incident is very recent, the cybercriminals are likely still trying to negotiate with the company before listing it on their site and threatening to leak stolen data.
Rackspace noted that it’s still early to say whether any data has been compromised. It likely depends on how long the attackers spent inside the company’s systems before the hack was detected.
“If we determine sensitive information was affected, we will notify customers as appropriate,” Rackspace said.
“Based on the investigation to date, we believe that this incident was isolated to our Hosted Exchange business. The Company’s other products and services are fully operational, and we have not experienced any impact to our Rackspace Email product line and platform,” it added.
Impacted Rackspace customers have been instructed to switch to Microsoft 365 for email services. The company said it managed to restore email services to thousands of customers on Microsoft 365.
Security researcher Kevin Beaumont believes the incident may involve exploitation of the Microsoft Exchange vulnerabilities tracked as CVE-2022-41040 and CVE-2022-41082, known as ProxyNotShell.
ProxyNotShell came to light in late September after a Vietnamese cybersecurity company saw it being exploited in the wild. Microsoft confirmed exploitation and linked it to a state-sponsored hacker group.
The tech giant rushed to share mitigations, but experts showed that they could be easily bypassed. Microsoft only released patches in November.
Beaumont noticed that a Rackspace Exchange server cluster that is currently offline was running a build number from August 2022 a few days prior to the incident disclosure. Considering that the ProxyNotShell vulnerabilities were only fixed in November, it’s possible that threat actors exploited the flaws to breach Rackspace servers.
Related: BEC Scammers Exploit Flaw to Spoof Domains of Rackspace Customers
Related: Over 80,000 Exchange Servers Still Affected by Actively Exploited Vulnerabilities















