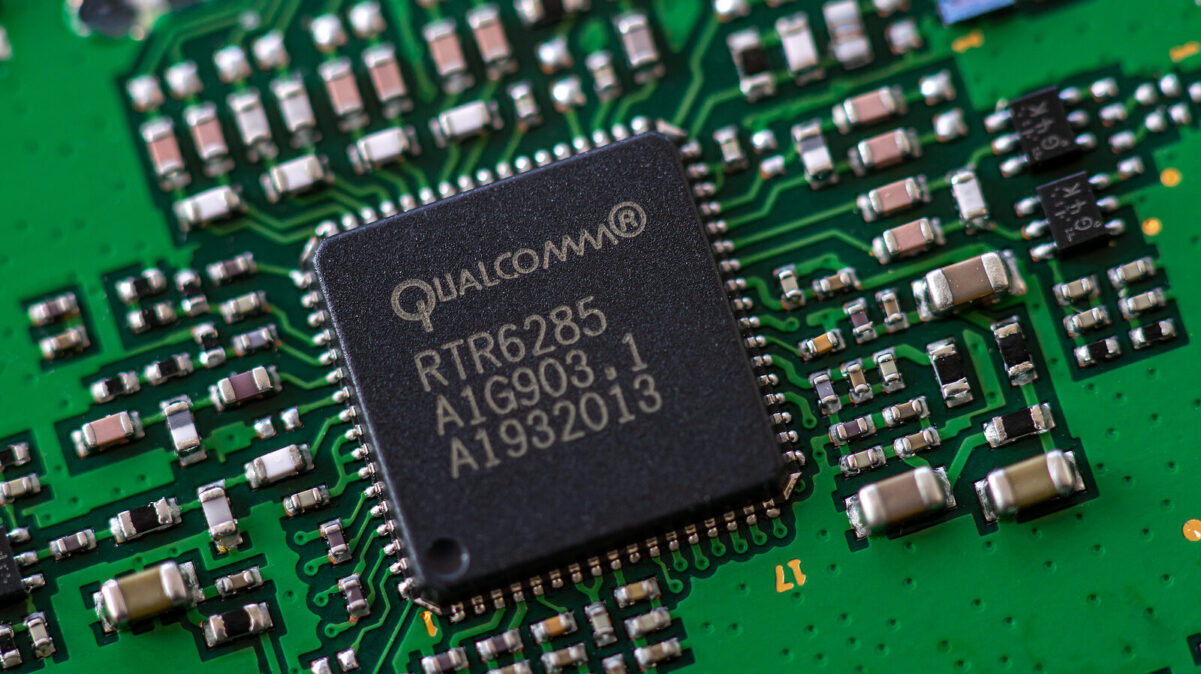
US chip giant Qualcomm this week announced patches for more than two dozen vulnerabilities found in its products, including three zero-days reported to the company by Google cybersecurity units.
Qualcomm learned from Google’s Threat Analysis Group and Google Project Zero that flaws tracked as CVE-2023-33106, CVE-2023-33107, CVE-2023-33063 and CVE-2022-22071 “may be under limited, targeted exploitation”.
However, only three of the flaws are zero-days as CVE-2022-22071 was patched by Qualcomm in May.
No information has been shared on the attacks exploiting these vulnerabilities, but the fact that they were reported by Google suggests that they may have been exploited by commercial spyware vendors.
Google has investigated several exploit chains attributed to spyware vendors in the past few years. Threat actors have been observed using such exploits to deliver spyware to devices running Android or iOS, both of which can include Qualcomm chips.
A vast majority of the remaining vulnerabilities for which patches were announced this week by Qualcomm have been assigned ‘critical’ and ‘high’ severity ratings, but they were discovered internally by the company.
Most of these security holes impact modems, WLAN firmware, and automotive products, and they have been described as memory bugs and information disclosure issues. Memory bugs can typically lead to arbitrary code execution or denial of service (DoS).
Also this week, Google released Android security updates that patch two zero-days, including CVE-2023-4211, a bug in the Arm Mali GPU driver that is known to have been targeted in attacks delivering spyware.
Related: Google Links Exploitation Frameworks to Spanish Spyware Vendor Variston
Related: Android’s June 2023 Security Update Patches Exploited Arm GPU Vulnerability
Related: Vulnerabilities in Qualcomm Chips Expose Billions of Devices to Attacks