The Qatar National Bank (QNB) has launched an investigation after someone leaked a large number of files allegedly stolen from the financial institution’s systems as a result of a hacker attack.
The leaked data, currently available from Cryptome and other sources, was first distributed via Twitter using several accounts that tweeted a global-files.net link to news outlets, journalists and others.
The leaked information, totaling roughly 1.5 Gb in size, consists of more than 15,000 files. The data includes banking information, payment card details, email addresses, passwords, physical addresses, phone numbers, and QNB user profiles.
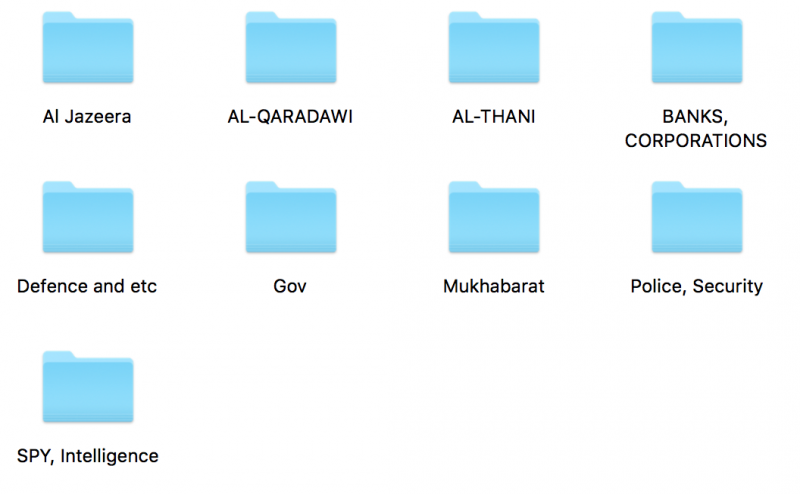
The user profiles, which in some cases contain photographs, are stored in folders whose names suggest that they are linked to government organizations, including intelligence agencies, in Qatar and other countries. One of the folders includes information on people working at Qatar-based media company Al Jazeera.
Security experts who analyzed the data said they believe it originates from QNB systems. Some speculated that the files might have been stolen by an insider.
In a statement published on Tuesday, QNB said it launched an investigation in coordination with “all concerned parties.”
“Referring to social media speculation in regard to an alleged data breach, it is QNB Group policy not to comment on reports circulated via social media. QNB would like to take this opportunity to assure all concerned that there is no financial impact on our clients or the Bank,” the bank said. “QNB Group places the highest priority on data security and deploying the strongest measures possible to ensure the integrity of our customers’ information.”
The news that the Qatar National Bank might have suffered a data breach comes just weeks after Bangladesh’s central bank announced that cybercriminals managed to steal over $100 million from one of its accounts at the Federal Reserve Bank of New York. The bank managed to recover some of the money, but $81 million that were transferred to the Philippines are still missing.
British defense, security and aerospace company BAE Systems revealed this week that the attackers appear to have used custom malware that allowed them to conduct fraudulent transfers without being detected.













