Pwn Pulse Combines “Hack-in-a-box” Sensors with Central Management for Remote Location Intelligence
Pwnie Express, the experts behind the network security testing platform that powers the Pwn Pad, Pwn Plug, and Pwn Phone, have launched a software-as-a-service (SaaS) version.
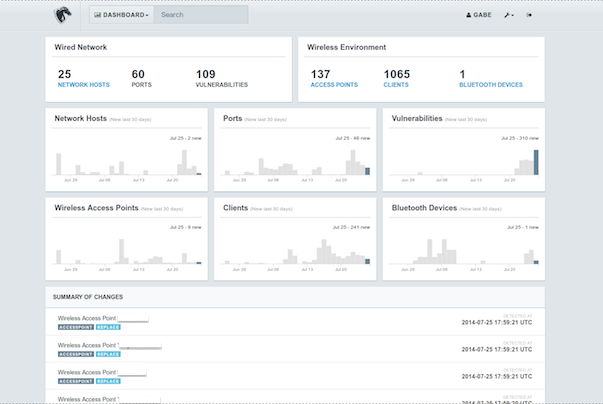
Called the Pwn Pulse, the platform allows network security professionals to deploy sensors and collect real-time information about the state of wired and wireless networks. Pwn Pulse allows real-time asset discovery for both wired and wireless assets, provides continuous vulnerability scanning, supplies penetration testing tools, and offers risk-trending and alerting capabilities, the Boston-based company said.
“Businesses have fortified their headquarters but the branch offices remain vulnerable,” Dave Porcello, CTO and founder of Pwnie Express, told SecurityWeek. Most organizations spend 90 percent of their security budgets to secure headquarters and 10 percent, or less, to protect remote locations, he said.
Attackers know the easiest way in is via the branch offices. Pwn Pulse is ideal for organizations with more than five locations, and is designed to scale, Porcello said.
Unlike its previous drop-box offerings, the end-to-end security assessment toolset is designed specifically for hard-to-reach remote sites. Pwn Plug, while it could be managed and accessed remotely, still required someone to be present at the site initially to plug it in. The Pwn Pad and Pwn Phone is more for the field staff, who would actually be on side. Pwn Pulse, on the other hand, is a cost-effective, lightweight, and non-intrusive platform that provides detailed information about what is happening at a remote location, without having to send dedicated IT staff out there.
The sensors are shipped out to the remote site, already configured to communicate back to the centralized console, and can be set up by anyone. It’s just a matter of plugging in power and connecting the Ethernet cable, Porcello said. “Bank representatives can do it, store managers can do it, anyone can do it,” he said.
Pwn Pulse’s asset discovery capabilities will particularly helpful, considering how challenging asset discovery is for remote locations. Many organizations, while they may be able to perform vulnerability management, penetration testing, and site assessments frequently at their main locations, struggle to maintain a consistent schedule for their remote sites. Pwn Pulse will expand the “awareness of wired, wireless, BYOD and rogue devices across all devices,” Pwnie Express said.
The Pwn Pulse’s centralized management console simplifies sensor deployment as it is out-of-the-box, across multiple sites, and provides trending and analysis of data collected by the sensors. It is also possible to drill down all the way to individual sensors, according to the company. The solution also integrates with existing security information and event management platforms the organizations may already have deployed within the enterprise.
Pwn Pulse also has a really interesting capability that will be particular useful for incident responders. The platform can detect mobile devices in the vicinity of the monitored assets, even if they are not connected to the network, Porcello said. For example, if there is a breach at an ATM, the administrator can use Pwn Pulse to see all the phones that were detected as being near the ATM. Or if a retailer was tracking someone malicious across multiple locations, the platform can show how the same phone has visited each of the affected sites.
“Show me all the phones that were in the vicinity of the breach,” Porcello said.
Pwn Pulse is currently in beta with general availability scheduled for the fourth quarter of this year.

