In late June, Symantec reported on a form of malware that had been launching junk print jobs and wasting paper until the printer runs out. Symantec calls the malware Milicenso, or the “Printer Bomb”, and code examination marks it as a variant of a malware delivery system discovered in 2010. Think of it as a malware system for hire, Symantec explained, noting that the payload most commonly associated with this Milicenso is Adware.Eorezo; an adware targeting French speaking users.
![]() Today, after conducting additional research on Trojan.Milicenso, Symantec determined that the threat is propagated by a compromised .htaccess file that launches a redirection Web attack. So far, Symantec has been able to count at least 4,000 websites that have been compromised by the cybercriminal(s) behind the attacks.
Today, after conducting additional research on Trojan.Milicenso, Symantec determined that the threat is propagated by a compromised .htaccess file that launches a redirection Web attack. So far, Symantec has been able to count at least 4,000 websites that have been compromised by the cybercriminal(s) behind the attacks.
In simple terms, as Symantec explains, an .htaccess file is configuration file used by Web servers that enable administrators to set certain controls such as restricting access to certain Web pages, redirecting access from mobile devices to special sites, etc.
“In order to monitor network traffic to legitimate websites, attackers (and some exploit kits) break into vulnerable Web servers and modify the .htaccess file,” Symantec explained.
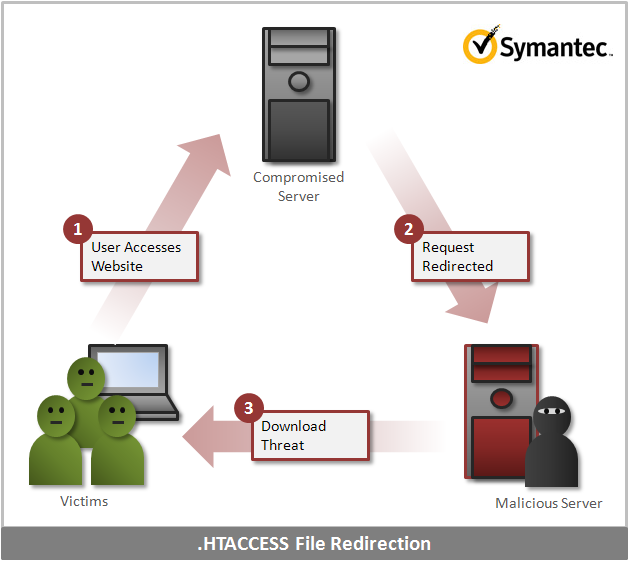
For this .htaccess file redirection attack, Symantec outline the process as follows:
1. When a user clicks the link for the website, the Web browser accesses the compromised website.
2. The Web server then redirects the access to a malicious website based on the .htaccess file.
3. The malicious site may then download more threats onto the compromised computer by exploiting certain vulnerabilities
In an effort to hide modifications made to the .htaccess file, Symantec noticed that the attackers inserted more then 800 empty lines of code both above and below the configuration settings in the file. Additionally, as Symantec reported in early analysis of the malware, it keeps itself encrypted to hinder analysis, and it goes through some internal system checks in order to ensure that the malware isn’t running on a VM or analysis engine such as Threat Expert.
Symantec’s research showed that the attack dated back to at least 2010, and the attacker(s) used different domain names to prevent them from being blocked or blacklisted. “In 2010 and 2011, the gang moved to a new domain every few months. But in 2012, they changed domains almost every day,” Symantec’s Kaoru Hayashi explained in a blog post.
“Within the last three days, we have identified approximately 4,000 unique, compromised websites that redirect users to malicious websites,” Hayashi added. “Most of the compromised websites are personal or SMB segment websites; but government, telecom, and financial service websites have also been compromised.”
A diagram from Symantec illustrating the infection process is below.