Russia is continuing its campaign of disinformation around the Ukraine war through advanced social engineering delivered by a threat group tracked as TA499.
According to a report from Proofpoint, TA499 targets US and European politicians, and leading businessmen and celebrities who have spoken out against Putin’s invasion. The primary purpose is to persuade the victims to take part in phone calls or video chats from which pro-Putin snippets can be elicited and published – thereby discrediting any previous anti-Putin comments.
It continues Russia’s efforts to fracture anti-Russian sentiment in North America and the EU with campaigns of disinformation. The European Parliament already contains numerous members opposed to any pro-Ukrainian activity – and Russia seeks to build on this.
TA499 appears to be a two-person group of operators publicly known as Vovan and Lexus. It is not known how closely they are tied to the Russian government. However, their operations are sophisticated, complex, and do not seem to be financially motivated. Proofpoint classifies them as ‘patriotically motivated’ and ‘aligned with the Russian state’.
The operation begins with TA499 making email or phone contact with their targets. Although this activity began before the invasion of Ukraine, “TA499’s campaigns began to ramp up in late January 2022, culminating in increasingly aggressive attempts after Russia invaded Ukraine in late February 2022,” say the researchers.
By March 2022, emails or phone calls began to masquerade as the Ukrainian Prime Minister Denys Shmyhal and his supposed assistant. Emails pretended to come from official embassies. with subjects such as ‘Prime Minister of Ukraine Request’. For example (although not proven, but assessed with ‘high confidence’, to be TA499), the UK Secretary of State for Defense, Ben Wallace, tweeted on March 17, 2022, “Today an attempt was made by an imposter claiming to be Ukrainian PM to speak with me. He posed several misleading questions and after becoming suspicious I terminated the call.”
Other approaches from TA499, pre-dating the Ukraine invasion, have targeted individuals that have made positive statements about the imprisoned Russian opposition leader Alexei Navalny – emails have masqueraded as messages from Leonid Volkov, Navalny’s chief of staff.
The purpose of such contacts is to persuade the target to join a telephone conversation or remote video call with TA499. If successful, the group engages in conversation with the attempt to elicit contradictory statements designed to discredit earlier anti-Kremlin statements. Proofpoint does not believe that TA499 has used deepfake technology in these exchanges, instead relying on an actor – for example, ‘Lexus’ pretended to be Volkov in Navalny-themed attacks.
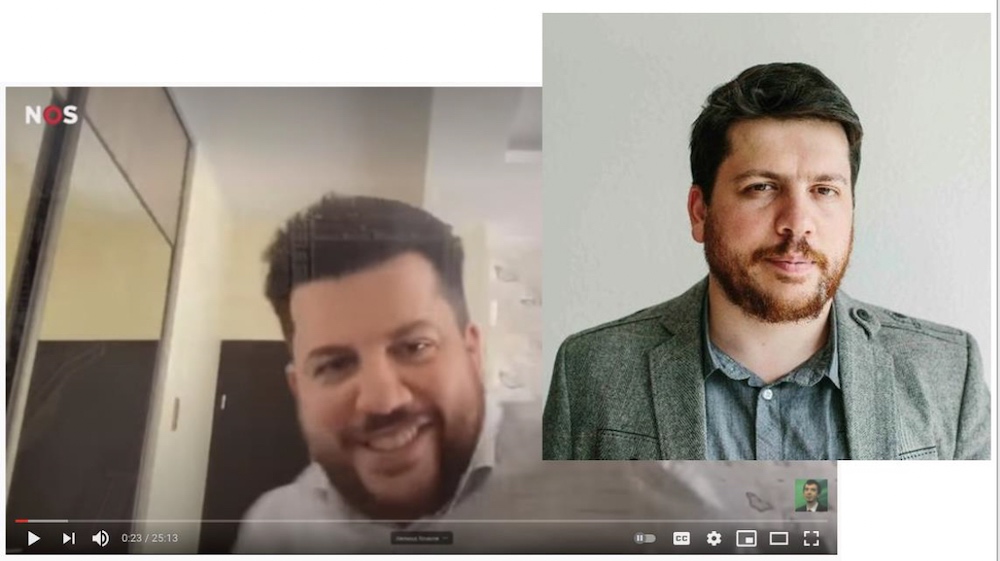
If successful, the recordings have been made public; for example, on YouTube and RuTube. “There are videos already publicly available of previous successful interactions,” the researchers told SecurityWeek. But they believe the YouTube recordings have already been taken down.
“According to open-source reporting, the following have been targets of the threat actor we track as TA499,” the researchers told SecurityWeek: “The mayor of Vienna Michael Ludwig, as well as other mayors in Warsaw, Budapest, Berlin, and Madrid. Celebrities JK Rowling and Elton John have also been targeted in the past.
“Overall, TA499 has not targeted based on government roles,” they continued, “but based on comments being made about the Russia-Ukraine war, general negative commentary about Russia and Putin, and involvement of government officials, celebrities, or prominent individuals running charities in support of Ukraine. “
Some reports have suggested that TA499 has used deepfake technology. Proofpoint cannot confirm this, but warns that even if they haven’t, they are likely to do at some point in the future. This threat, and other similar threats, will only become more effective as the technology improves. “There is a likelihood that if TA499 has not already adopted deepfakes, they will at some point,” said the researchers.
It is possible that TA499 started as a patriotic prankster group. “They have personas that not only post the material discussed in this report online but also perform reenactments on Russia state-sponsored media as well as attend conferences,” says Proofpoint “With the war between Russia and Ukraine unlikely to end in the near-term and Ukraine continuing to garner support from organizations worldwide, Proofpoint assesses with high confidence that TA499 will attempt to continue with its campaigns in support of its influencer content and political agenda.”
The war has given pranks a serious and damaging incentive. So far, it is likely that this has been achieved without the use of deepfake technology. It is, however, a clear warning on the likelihood of even more compelling social engineering attacks in the future.
Related: Deepfakes – Significant or Hyped Threat?
Related: The Lessons From Cyberwar, Cyber-in-War and Ukraine
Related: Russian Espionage APT Callisto Focuses on Ukraine War Support Organizations
Related: A Year of Conflict: Cybersecurity Industry Assesses Impact of Russia-Ukraine War

