A researcher has released proof-of-concept (PoC) exploits for unpatched same-origin policy bypass vulnerabilities affecting Microsoft’s Internet Explorer and Edge web browsers.
James Lee, who focuses on vulnerability research, made the PoC exploits public last week. He said he had reported his findings to Microsoft 10 months ago, but received no reply and the flaws remain unpatched.
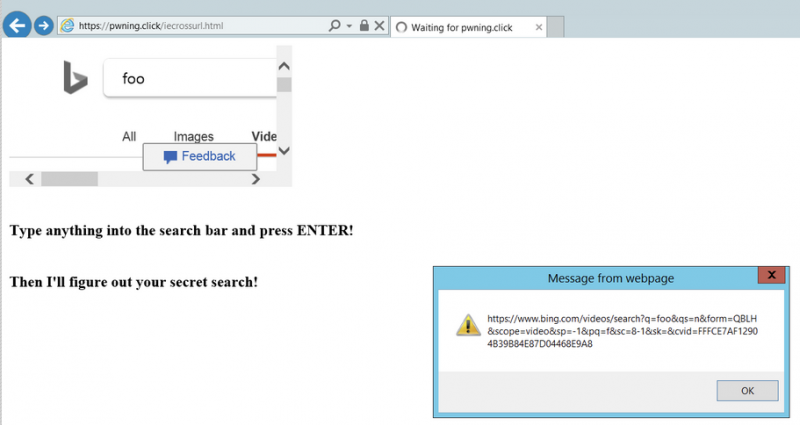
The security holes can be exploited by a malicious website opened in Internet Explorer or Edge to collect potentially sensitive information from other sites visited by the targeted user.
The same-origin policy (SOP) mechanism should prevent websites from interacting with each other, but security researchers occasionally find ways to bypass it.
An analysis conducted by experts at Trend Micro shows that the vulnerabilities can be exploited by a malicious site to gain access to any information stored in another website’s URL, even if the information should be hidden.
“Examples of vulnerable information that might be stored in the URL include cookies, sessionIDs, usernames, passwords, and OAUTH tokens, either in plaintext or hash form. OAUTH is a way of authorizing third party applications to login to users’ online accounts, and has a history of being abused. Any sensitive information included in the URL of a website could be collected using these vulnerabilities,” Trend Micro explained in a blog post.
It’s unclear why Microsoft has not patched these vulnerabilities. SecurityWeek has reached out to the company for comment and will update this article if it responds.
Lee has promised to publish a blog post describing his findings soon, but as Trend Micro’s analysis shows, the PoC exploits are more than enough for someone to work out the details.
This is not the first time a researcher has disclosed a SOP bypass flaw in Microsoft’s browsers after the company failed to release a patch.
It’s also not uncommon for vulnerabilities affecting Microsoft products to be exploited in the wild and an analysis conducted recently by Recorded Future showed that eight of the top ten most exploited flaws in 2018 affected the company’s software.
UPDATE. Microsoft told SecurityWeek it’s not concerned about the impact of these vulnerabilities.
Related: Websites Can Exploit Browser Extensions to Steal User Data
Related: Windows Servers Vulnerable to DoS Attacks, Microsoft Warns
Related: Microsoft Patches Internet Explorer Zero-Day Reported by Google














