Tools advertised as being capable of cracking passwords for HMIs, PLCs and other industrial products have been found to exploit a zero-day vulnerability, and threat actors are using these tools to deliver malware.
Engineers responsible for the industrial systems within an organization may one day find themselves in a situation where a PLC, an HMI or a project file that needs to be updated is protected by a password they don’t know — the password may have been forgotten or set by someone who has left the company.
Searching the web for a solution can lead engineers to websites advertising tools that are designed to crack passwords for specific industrial products.
An analysis conducted by industrial cybersecurity company Dragos shows that such password cracking tools can also deliver malware.
Dragos has investigated a tool designed for DirectLogic PLCs from AutomationDirect, but the same threat actor also offers password cracking software for several other products from Omron, Siemens, ABB, Delta Automation, Fuji Electric, Mitsubishi Electric, Pro-face (Schneider Electric), Vigor, Allen-Bradley (Rockwell Automation), Panasonic, LG, Fatek, and IDEC.
A brief analysis suggests that these other tools likely also deliver malware and Dragos noted that similar tools have been offered by others as well.
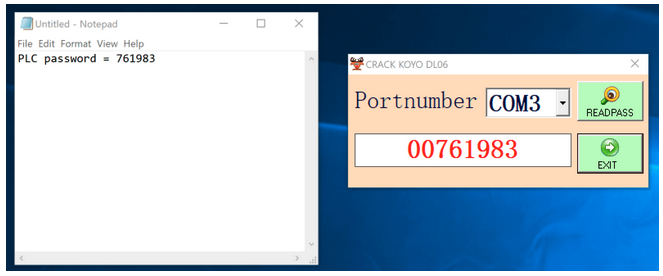
The DirectLogic PLC cracking tool did return the device’s password and it did so by exploiting a previously unknown vulnerability. The flaw, tracked as CVE-2022-2003, can be exploited to cause the PLC to provide its password in clear text in response to a specially crafted request sent over Ethernet or the serial port.
AutomationDirect has patched this and a DoS vulnerability after being notified by Dragos. CISA has released two advisories to inform organizations about the security holes.
The password cracking tool analyzed by Dragos delivered the well-known Sality malware, which has been around for two decades, often being used by cybercriminals for financial gain.
While threat actors could in theory use the access provided by Sality to disrupt industrial processes, the cybersecurity firm believes the group distributing these tools is financially motivated and it’s trying to make a profit through cryptocurrency theft.
While it may not target operational technology (OT) systems directly, Sality has been known to block resources related to antimalware products and this could have regulatory implications in the case of industrial organizations.
“Since Sality blocks any outgoing connections, antivirus systems will not be able to receive updates violating reliability standard CIP-007-6,” Dragos explained.
Related: Thousands of Industrial Firms Targeted in Attacks Leveraging Short-Lived Malware
Related: Ransomware Often Hits Industrial Systems, With Significant Impact

