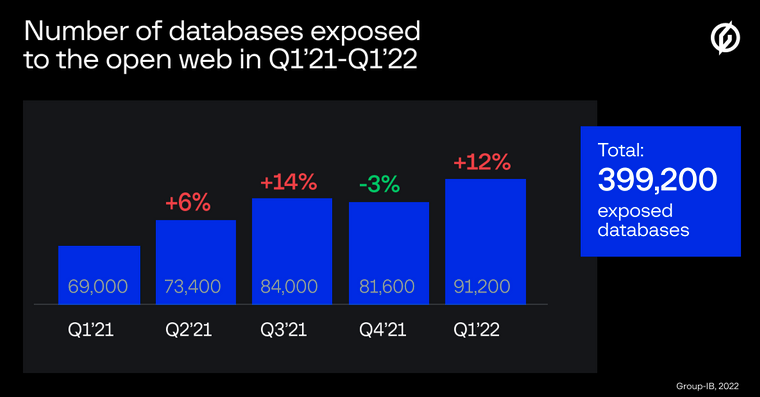
Cybersecurity firm Group-IB identified more than 91,000 publicly-exposed databases in the first quarter of 2022, significantly more than in the previous year.
In 2021, the firm discovered a total of 308,000 exposed databases, with more than 165,000 of them found in the second half of the year. Most of the exposed databases use the Redis database management system (37.5%), followed by MongoDB (31%) and Elastic (29%).
Netenrich principal threat hunter John Bambenek pointed out to SecurityWeek that Group-IB’s report documents databases that can be accessed from the internet, rather than instances that have already been breached.
“However, this does not mean you can simply dump the contents without credentials or a vulnerability. While it is best practice not to ever have databases accepting connections from the Internet, it also does not mean immediate data loss,” Bambenek said.
Improperly inventoried internet-facing assets such as databases could be exploited in cyberattacks, leading to costly data breaches, Group-IB notes.
Last year, IBM found that the average cost of a data breach exceeded $4.2 million during the COVID-19 pandemic, up 10% from the previous year. The average time to identify and address a breach had increased as well, to 287 days.
While the number of exposed databases has increased, the time it takes for a database owner to fix the issue has remained the same as a year ago, at 170 days, the cybersecurity firm says.
“When it comes to management of high-risk digital assets, timely discovery plays a key role as threat actors are quick in spotting a chance to steal sensitive information or advance further in the network,” Group-IB notes.
[ READ: Attacker Dwell Times Down, But No Consistent Correlation to Breach Impact]
In most cases, Bambenek points out, securing a database requires only minor configuration changes that require minimum effort. However, he also notes that proper hardening of cloud instances right from the start often significantly reduces efforts after the fact.
Vulcan Cyber senior technical engineer Mike Parkin too points out that configuration issues are those that typically cause cybersecurity issues, in spite of efforts to address the situation.
“Making sure a database is configured securely from the start adds only a trivial amount of time but can lead to massive savings later,” Parkin said. “In most cases, there’s no need to expose a database directly to the internet as a whole. When they do need to be exposed, there are platform specific configurations that can make it much safer.”
Group-IB’s researchers also say that the largest number of identified exposed databases (93,600) were found on servers located in the United States. China (with 54,700 exposed databases) and Germany (11,100) round up the top three.
“With the growth of DevOps practices has come the growth in ignoring best practices. That said, I imagine most of these instances are development instances with (hopefully) test data or embedded devices that aren’t storing customer data in the first place,” Bambenek pointed out.
Related: Gh0stCringe RAT Targeting Database Servers in Recent Attacks
Related: Cybersecurity Firm Exposes Breach Database Containing 5 Billion User Records
Related: Nearly Half of On-Premises Databases Vulnerable to Attacks: Study














