The Open Source Security Foundation (OpenSSF) announced on Wednesday at the Black Hat Europe conference the availability of an open source tool designed for evaluating the ability of static analysis security testing (SAST) products to detect vulnerabilities.
The new tool, named OpenSSF CVE Benchmark, provides vulnerable code and metadata related to 218 known JavaScript and TypeScript vulnerabilities.
The tool can be integrated with ESLint, CodeQL and NodeJsScan, but its creators hope the community will help build integrations with more security tools and help expand the dataset. The developers pointed out that less than 200 lines of code are typically required to create a new security tool integration, and they believe it can be easily integrated with not only open source tools, but also commercial products.
The goal of the tool, whose source code is available on GitHub, is to make it easier for security teams to evaluate various SAST tools. Specifically, it helps determine if a security tool can detect a vulnerability or if it produces a false negative, and whether it can recognize a validated patch or it produces a false positive
.
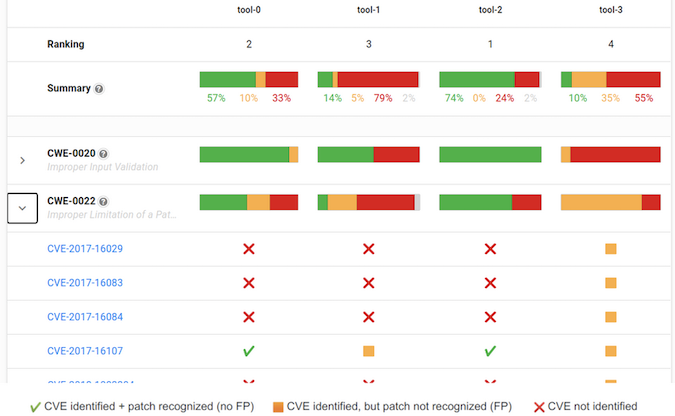
“The benchmark addresses two problems that security teams face today when assessing security tools. First, rather than using synthetic test code, the OpenSSF CVE Benchmark uses real life CVEs that have been validated and fixed in open source projects. Using this approach, security tools are tested on real codebases that contain validated real vulnerabilities,” the developers explained.
“Second, by also analyzing the patched versions of the same codebases, false positive rates of these tools can be measured more accurately and based on real validated fixes,” they added.
Launched in August 2020 and hosted by the Linux Foundation, OpenSSF aims to improve the security of open source software by building a community, best practices and targeted initiatives. Its members include GitHub, IBM, Google, VMware, Microsoft, NCC Group, OWASP, JPMorgan Chase, Red Hat, Intel, HackerOne, Uber, GitLab, Okta and others.
Related: StackRox Releases Open Source Tool for Finding Kubernetes Misconfigurations
Related: GrammaTech Releases Open Source API Security Tool
Related: Adobe Open Sources Tool for Sanitizing Logs, Detecting Exposed Credentials












