Decoy documents used in two recent cyber espionage campaigns apparently aimed at entities linked to North Korea show a connection between the DarkHotel attacks and a piece of malware named KONNI.
KONNI is a remote access trojan (RAT) that managed to stay under the radar for more than 3 years. The malware has evolved over the past years and it’s currently capable of logging keystrokes, stealing files, capturing screenshots, and collecting information about the infected machine.
KONNI has mainly been used to target organizations linked to North Korea. One of the campaigns spotted by researchers at Cisco Talos this year involves a dropper named “Pyongyang Directory Group email April 2017 RC_Office_Coordination_Associate.scr,” which opens a Word document when executed.
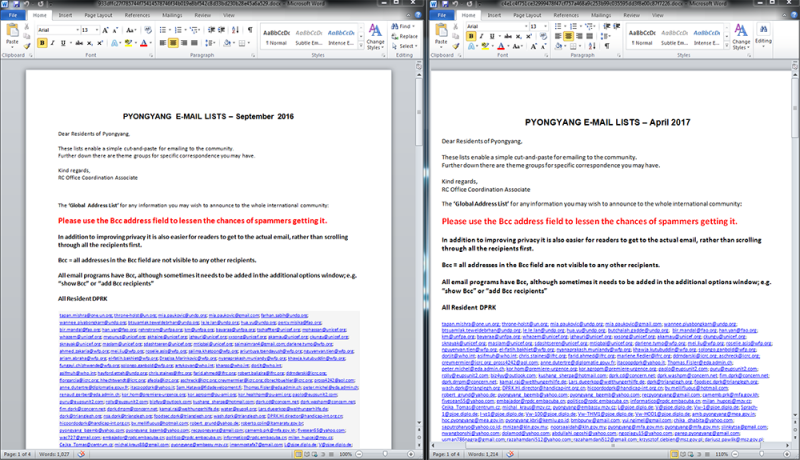
Researchers at Cylance noticed that this decoy document, titled “Pyongyang e-mail lists – April 2017,” is very similar to a document delivered in a recent campaign linked by Bitdefender to DarkHotel, a threat group that has been around for nearly a decade.
DarkHotel came to light in November 2014, when Kaspersky published a report detailing a sophisticated cyber espionage campaign targeting business travelers in the Asia-Pacific region. The group, whose members appear to be Korean speakers, possibly from South Korea, has targeted individuals in North Korea, Russia, South Korea, Japan, Bangladesh, Thailand, Taiwan, China, the United States, India, Mozambique, Indonesia and Germany.
The new DarkHotel campaign analyzed by Bitdefender, dubbed “Inexsmar” by the security firm, was aimed at government employees with an interest in North Korea. One of the decoy documents used in the attack is very similar to the one seen in the KONNI attacks – it’s titled “Pyongyang e-mail lists – September 2016” and its content has the same format.
Furthermore, an analysis of the files’ description revealed that they are both titled “Pyongyang directory” and they were both authored by an individual named “Divya Jacob.”
Cylance has conducted a detailed analysis of KONNI and the company’s experts believe that, as a result of the recent attention, the malware’s authors will release new variants that will include better obfuscation and additional capabilities.
Related: North Korea-Linked Hacker Group Poses Serious Threat to Banks
Related: Kaspersky Links Global Cyber Attacks to North Korea