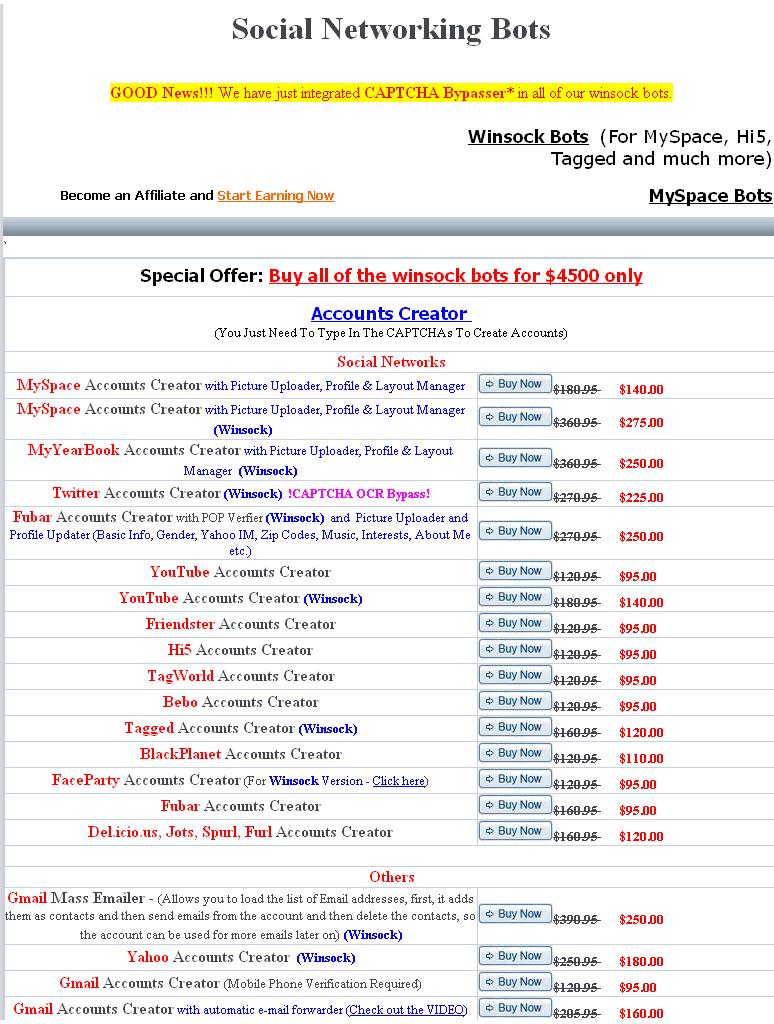
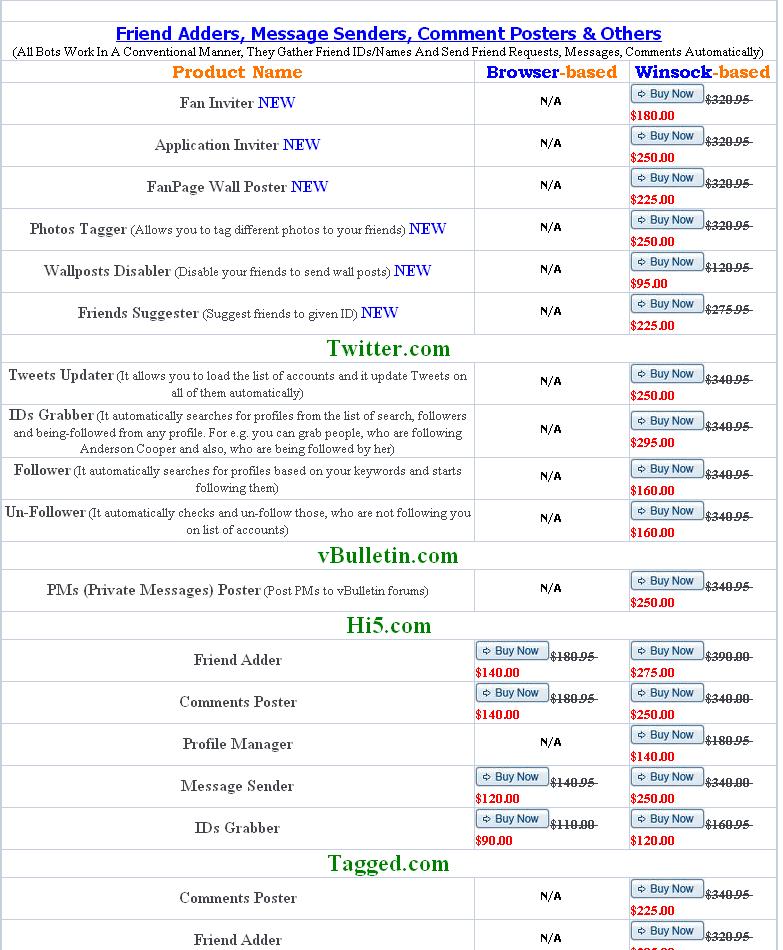
• Internet portal offers bots designed for various activities at prices ranging from $95 to $225; entire catalog of bots costs $4,500
• Creators claim that all bots are undetectable, as they randomly change users, agents and headers; also include automated CAPTCHA generators
PandaLabs, the anti-malware laboratory of Panda Security, today discovered a network selling bots specialized in targeting social networks and webmail systems. The publicly available Web page contains an extensive catalog of programs aimed at social networks and webmail services including Twitter, Facebook, Hi5, MySpace, MyYearBook, YouTube, Tuenti, Friendster, Gmail and Yahoo.
Each entry explains the reason for which the bot has been created and offers activities that the bots can perform such as creating multiple accounts simultaneously on social networks; identity theft and stealing friends, followers or contacts; automatic sending of messages, etc. According to the page, “All Bots Work In A Conventional Manner, They Gather Friend IDs/Names and Send Friend Requests, Messages, Comments Automatically.”
Luis Corrons, Technical Director of PandaLabs states, “We are still investigating, but this is another example of the lucrative business that malware represents for cyber-criminals. The catalog of bots for sale describes some of the many activities they can be used for. Some of them are more ‘innocent’ such as creating accounts and others more insidious and specifically focused on fraud, including theft of identities, photographs, etc.”
Prices range from $95 for the cheapest bot to $225 for the most expensive. The entire catalog can be purchased for $4,500, and the site guarantees that they will never be detected by any type of security solution, claiming they have been developed to change users, agents and headers as many times as is necessary to prevent from being blocked. They also have round CAPTCHA security mechanisms included on many websites, so the buyer just has to set the parameters and leave the bots to operate on their own. The bots also include perpetual updates.
Some of the more unusual activities for which the bots have been designed include:
• An automatic generator of visits and views for YouTube videos
• Optimization of rankings in Alexa
• Vote tampering in Digg
• Unlimited sending of messages on online dating sites such as DirectMatches
The bots are specially adapted for each website, and the list of targets includes not just globally popular social networks or communities, but also regional sites such as Tuenti, Yahoo UK, etc.
“On the same portal, there is also an offer to earn money by reselling these ‘products’ as an affiliate. It is these kinds of models that help build cyber-mafias and organizations that operate across several countries. We should still not forget, however, that this business exists not just because there are developers creating the threats, but also because there are criminals who are prepared to pay for them. Until we are able to prevent people from defrauding victims in this way, this business model will continue to thrive,” concludes Luis Corrons.
Panda Labs was able to capture the screenshots below: