Cybercriminals have been leveraging a new technique, which involves PowerPoint files and mouseover events, to get users to execute arbitrary code on their systems and download malware.
It’s not uncommon for malicious actors to deliver malware using specially crafted Office files, particularly Word documents. These attacks typically rely on social engineering to trick the targeted user into enabling VBA macros embedded in the document.
However, researchers recently spotted several malicious PowerPoint files that use mouseover events to execute PowerShell code. These files, named “order.ppsx” or “invoice.ppsx,” have been distributed via spam emails with subject lines such as “Purchase Order #130527” and “Confirmation.”
An analysis conducted by Ruben Daniel Dodge shows that when the PowerPoint presentation is opened, it displays the text “Loading…Please wait” as a hyperlink.
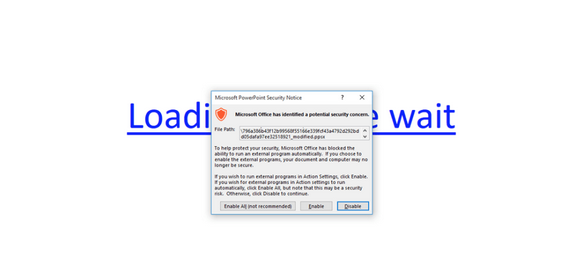
If the user hovers the mouse over the link – even without clicking it – the execution of PowerShell code is triggered. The Protected View security feature, which is enabled by default in most supported versions of Office, informs the user of the risks and prompts them to enable or disable the content.
If the victim enables the content, the PowerShell code is executed and a domain named “cccn.nl” is contacted. A file is downloaded from this domain and executed, ultimately resulting in the deployment of a malware downloader.
Researchers at SentinelOne have also analyzed the attack and found that it had been used to deliver a new variant of the banking Trojan tracked as Zusy, Tinba and Tiny Banker.
The security firm pointed out that while the attack does not work if the malicious presentation is opened using PowerPoint Viewer, and most versions of Office warn the user before the code is executed, the method could still be efficient in some cases.
“Users might still somehow enable external programs because they’re lazy, in a hurry, or they’re only used to blocking macros. Also, some configurations may possibly be more permissive in executing external programs than they are with macros,” SentinelOne Labs said in a blog post.
Related Reading: Macro Malware Comes to macOS
Related Reading: Office Loader Uses Macros to Drop Array of Malware
Related Reading: Macro Malware Makes Improvements on Hiding Malicious Code















