A group of academic researchers has devised a new eavesdropping attack that leverages the lidar sensors present in commodity robot vacuum cleaners.
Dubbed LidarPhone, the attack relies on traces of sound signals that are extracted from laser reflections to capture privacy sensitive information, including speech during teleconference sessions. It could also be used to spy on a victim’s TV habits and perhaps identify their political orientation.
Devised by a group of five researchers from the National University of Singapore and University of Maryland, College Park, the attack “achieves approximately 91% and 90% average accuracies” when used to collect spoken digits and music, respectively.
This novel acoustic side-channel attack is possible because the vacuum cleaning robot, a seemingly innocuous household device, is equipped with lidar sensors, which help it measure the distance to different objects by emitting laser light and measuring its reflection.
Sounds, the researchers explain, are pressure waves propagating through the medium’s vibrations, which are induced to surrounding objects. Thus, subtle physical vibrations are created within the solid material.
“The fundamental concept of LidarPhone lies in sensing such induced vibrations in house hold objects using the vacuum robot’s lidar sensor and then processing the recorded vibration signal to recover traces of sounds,” the researchers explain.
The same method is used by laser microphones and basically LidarPhone transforms the lidar sensors on the vacuum cleaning robot into microphones. Challenges that the new attack faces, however, include the low signal-to-noise ratio (SNR) of the reflected signals and the lidar’s low sampling rate, due to the robot’s rotating motion.
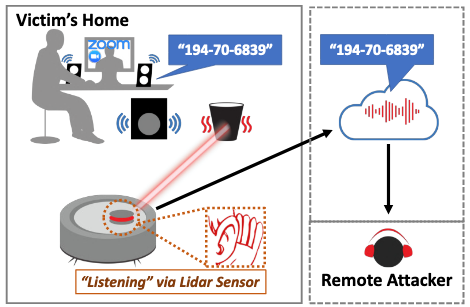
According to the researchers, some of the main limitations of this attack include the fact that the intensity of sound vibrations is lower when objects are not in direct contact with the speakers, and the fact that the robot is continuously moving when operational — thus, it is more plausible to launch an attack when the robot is idle.
The researchers implemented LidarPhone on a Xiaomi Roborock vacuum cleaning robot and concluded that it can achieve high accuracy for digit and music classification. They also argue that, unlike state-of-the-art eavesdropping attacks where physical presence is required to deploy the surveillance equipment, LidarPhone eliminates this step — the attacker only needs to somehow compromise the targeted vacuum.
“LidarPhone allows the adversary to obtain privacy sensitive speech information from laser beams reflected off of minutely vibrating objects (such as a trashcan or a takeaway bag) located near the victim’s computer speaker or TV soundbar. […] While we investigate lidars on robot vacuum cleaners as an exemplary case, our findings may be extended to many other active light sensors including smartphone time-of-flight sensors,” the researchers say.
Related: New Eavesdropping Technique Relies on Light Bulb Vibrations
Related: Power Supply Can Turn Into Speaker for Data Exfiltration Over Air Gap
Related: Air-Gapped Computers Can Communicate Through Heat: Researchers

