According to Microsoft’s 2022 Digital Defense Report, nation-state hacker attacks on critical infrastructure have soared, largely due to Russian cyber operations targeting Ukraine and its allies.
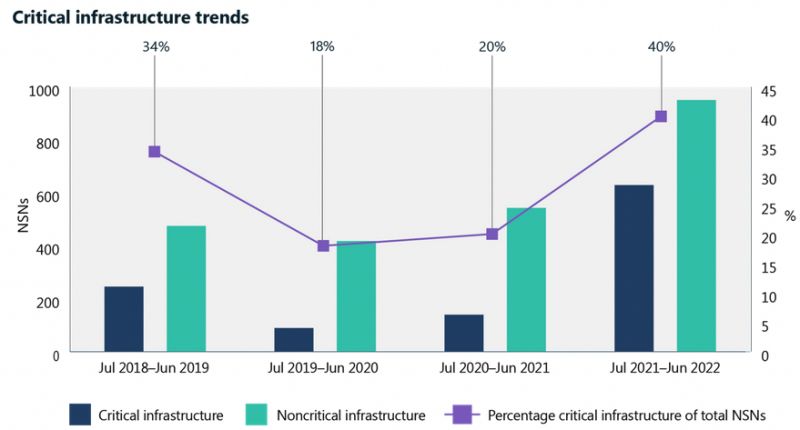
Between June 2020 and June 2021, 20% of all nation-state attacks observed by Microsoft were aimed at critical infrastructure. That percentage increased to 40% in the period between July 2021 and June 2022.
Many of the state-sponsored attacks targeting critical infrastructure in the past year have been attributed by the tech giant to Russia. Unsurprisingly, Russia has increasingly targeted Ukrainian critical infrastructure with cyberattacks meant to cause damage and disruption — this was done to complement its physical military action.
During this period, the world learned about the existence of two sophisticated pieces of malware designed to target industrial control systems (ICS). They have been named Pipedream (Incontroller) and Industroyer2, and they have both been linked to Russia.
In addition, the United States and other Ukrainian allies — many of them NATO countries — have also been increasingly targeted as part of espionage operations.
“Russia also accelerated its attempts to compromise IT firms as a way to disrupt or gain intelligence from those firms’ government agency customers in NATO member countries. 90% of Russian attacks we detected over the past year targeted NATO member states, and 48% of these attacks targeted IT firms based in NATO countries,” Microsoft said.
Other critical infrastructure sectors targeted by threat actors include financial services, transportation systems, and communications infrastructure.
Russia was not the only nation state targeting critical infrastructure. Iran has increasingly targeted the IT industry, as well as other critical infrastructure sectors, including in the United States.
“Iranian actors escalated bold attacks following a transition of presidential power. They launched destructive attacks targeting Israel, and ransomware and hack-and-leak operations beyond regional adversaries to US and EU victims, including US critical infrastructure targets like port authorities. In at least one case, Microsoft detected an attack disguised as a ransomware attack that was intended to erase Israeli data. In another, an Iranian actor executed an attack that set off emergency rocket sirens in Israel,” Microsoft said.
North Korea has continued targeting financial and technology companies in an effort to steal cryptocurrency.
Microsoft has also seen China expanding its global cyberespionage operations. Chinese threat actors often rely on zero-day vulnerabilities to achieve their goals, and Microsoft believes that a law requiring Chinese entities to report discovered vulnerabilities to the government may significantly contribute to this.
“The increased use of zero days over the last year from China-based actors likely reflects the first full year of China’s vulnerability disclosure requirements for the Chinese security community and a major step in the use of zero-day exploits as a state priority,” the company said.
Microsoft’s report also provides data on cybercriminal activity, influence operations, device and infrastructure attacks and threats, and cyber resilience. The full Microsoft Digital Defense Report 2022 is available in PDF format.
Related: Iranian Group Targeting Israeli Shipping and Other Key Sectors
Related: Microsoft Links Exploitation of Exchange Zero-Days to State-Sponsored Hacker Group













