Researchers at Avast have conducted a brief analysis of OmniRAT, a multi-platform remote administration tool (RAT) that has been used for malicious purposes.
OmniRAT is openly promoted as a remote administration tool that works on devices running Android, Windows, Linux and Mac OS X. OmniRAT servers and clients are currently sold for $25 and $50, a price that includes a lifetime license and lifetime support.
The tool, which is allegedly made in Germany, is not advertised for malicious purposes, but experts from Avast have seen it being distributed and used by cybercriminals as a remote access Trojan.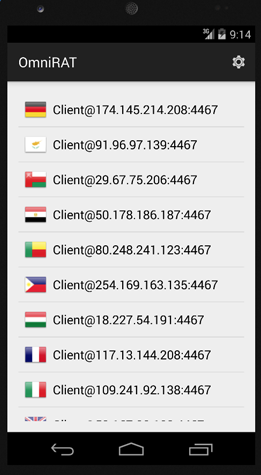
In an attack described on a German tech forum, a user reported that his Android device became infected with what Avast researchers determined to be OmniRAT. In a blog post published on Thursday, Avast mobile malware analyst Nikolaos Chrysaidos revealed that the threat has been distributed via social engineering.
In the case of the German user, the attackers sent him an SMS claiming that he had received an MMS that cannot be sent directly due to the Android StageFright vulnerability, for which experts had previously warned that exploits could be delivered via MMS.
The malicious SMS contained a shortened link pointing to a website where the victim was instructed to enter a code and their phone number. Once the code and the number were entered, victims had been served an APK that loaded an icon labeled “MMS Retrieve” when installed. The OmniRAT installation process would begin when this icon was tapped.
Chrysaidos has pointed out that in such cases the malware is not installed automatically, but instead the victim has to manually install it and accept a long list of permissions that it requests.
“The victim then has no idea their device is being controlled by someone else and that every move they make on the device is being recorded and sent back to a foreign server,” Chrysaidos said. “Furthermore, once cybercriminals have control over a device’s contact list, they can easily spread the malware to more people. Inside this variant of OmniRat, there is a function to send multiple SMS messages. What makes this especially dangerous is that the SMS spread via OmniRat from the infected device will appear to be from a known and trusted contact of the recipients, making them more likely to follow the link and infect their own device.”
In the case of the German user who reported the OmniRAT attack, the data collected from the infected device was sent back to a command and control (C&C) server in Russia.
OmniRAT is similar to DroidJack, a RAT that was initially developed as a legitimate application for remotely controlling Android devices, but was later turned by its creators into a crimeware tool. Symantec reported in November 2014 that it had traced the developers of DroidJack, whose retail price is $210, to India.
Last month, authorities in five European countries launched an operation against people who had acquired and used DroidJack to spy on others.
















