A majority of organizations that have operational technology (OT) infrastructure experienced at least one damaging cyberattack in the past two years, according to a survey conducted by Ponemon Institute and Tenable.
The study is based on responses from over 700 IT and IT security decision makers in the United States, United Kingdom, Germany, Australia, Mexico and Japan. Respondents represented the energy and utilities, industrial and manufacturing, health and pharmaceutical, and transportation sectors.
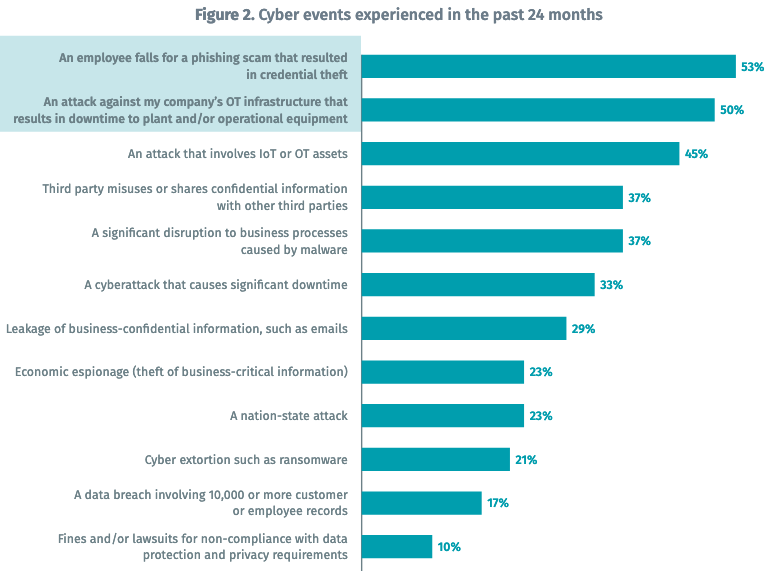
The report shows that 90% of respondents admitted suffering at least one damaging cyberattack in the past two years, and nearly two-thirds were hit at least two times. These statistics include attacks on IT systems, which are still relevant as attackers may be able to move from IT to OT systems.
Half of respondents said they had experienced an attack on their OT infrastructure that resulted in downtime of the plant and/or operational equipment. Many organizations also admitted suffering significant business disruptions and downtimes as a result of cyberattacks.
Furthermore, nearly a quarter of respondents believed they had been targeted by a nation-state actor.
Downtime to OT systems is the number one factor when quantifying cyber risk, with 49% of respondents citing it as a factor. Organizations also assess risk based on the frequency of unpatched vulnerabilities (45%), theft of intellectual property (41%), loss of employee productivity (40%), and financial loss (38%).
Learn More About OT Security at SecurityWeek’s 2019 ICS Cyber Security Conference
Companies are most concerned about a third party sharing or misusing confidential information, an attack on IT or OT assets, and an attack on OT systems that results in downtime. They are least concerned about nation-state attacks, ransomware, and fines or lawsuits stemming from non-compliance with privacy and data protection requirements.
Respondents said their number one governance-related priority for 2019 is to increase communications with C-level executives and boards (70%), followed by ensuring that third parties are capable of protecting sensitive and confidential data (63%), increasing employee cybersecurity training (59%), and allocating more resources to vulnerability management (55%).
As for security priorities for this year, two-thirds named improving their ability to keep up with adversaries. Roughly half of respondents also hope to reduce the risk of attacks on OT infrastructure, improving data security, and reducing IT security complexity.
Vulnerability management remains a problem for many organizations, the report shows. Only 20% of respondents said they had sufficient visibility into their attack surface, and over half of them admitted that manual processes create response backlogs and put them at a disadvantage.
Related: USB Drives Deliver Dangerous Malware to Industrial Facilities
Related: Many ICS Vulnerability Advisories Contain Errors
Related: Plaintext Passwords Often Put Industrial Systems at Risk














