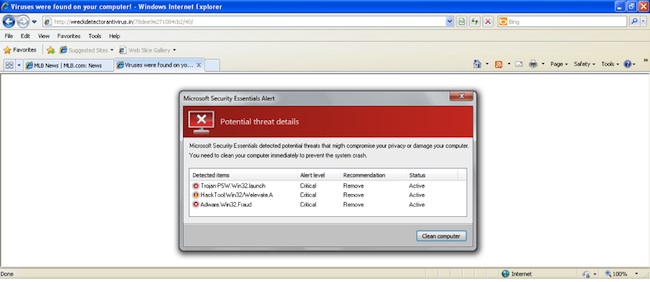
Just days after several large Web-based organizations united to fight malicious online ads, MLB.com was spotted serving malicious ads and directing visitors to Rouge Anti-Virus.
Rogue Anti-Virus applications actually generate decent income for some of the criminals who spread them, as they are paid for getting someone to install it, and will sometimes take a cut of the fee if someone registers it.
Once installed on a system the Rogue AV hinder performance, block access to various websites and security applications, as well as open the system for further malicious downloads. If the fake software is registered, not only is there a loss of money, but any personal information submitted during the registration process should be considered compromised too.
In the past, several high profile sites have fallen victim to malicious advertising techniques, where criminals register accounts on legit ad networks, going to far as to run legit ads for a while, and then once in rotation, the legit ads are traded for malicious ones. Once this happens, anyone visiting the domain that happens to come across the ad will be redirected to Rogue AV or any other malicious content the criminal chooses.
In 2009, the New York Times fell victim to an ad-network attack, forcing them to post a notice on the front page of their website. A month later, Gizmodo faced a similar problem. The attack on Gizmodo was one of the first to have a published account on how such scams work. In another high profile malvertising incident, the Web site for the London Stock Exchange was found to have been serving ads from a malicious network in early 2011. The list goes on and on.
It is unfortunate that on Monday, MLB.com became a statistic as they joined the list of high-profile websites to be caught in an advertising scam that led to an attack on their users. Perimeter E-Security, an information security services firm, reported that they had discovered Rogue AV was targeting some of their clients after visiting Major League Baseball’s official portal.
“Over the past week, we noticed that several customers who attempted to download various “fake antivirus” malware had accessed MLB.com immediately before the installation attempt. We suspected a polluted ad network, but needed the proof. After page-refreshing MLB.com 20–30 times we were finally given the [malicious] redirect…,” their report explains.
As mentioned, word of the MLB.com hijacking comes just days after Web giants including Google, AOL, Facebook, Twitter, and the Interactive Advertising Bureau (IAB) teamed-up to form the Ads Integrity Alliance.
“The Ads Integrity Alliance is a natural extension of StopBadware’s mission to make the Web safer by combating badware,” said the nonprofit organization’s executive director, Maxim Weinstein. “No one can address Internet-scale threats on their own, so we’re bringing together industry leading organizations to tackle the problem collaboratively.”
More information on the newly minted alliance is here. At the time of this story, SecurityWeek was unable to determine if MLB.com was still serving the malicious ads. Representatives were not available for comment.















