Japanese electronics and electrical equipment giant Mitsubishi Electric Corporation on Monday unveiled new technology designed to protect connected vehicles against cyber threats.
Many modern vehicles include communication features that allow connections to the Internet and mobile devices. While these features can be highly useful, they can also introduce cybersecurity risks.
Researchers have demonstrated on several occasions over the past years that connected cars can be hacked. Attacks, including ones that can be launched remotely, have been demonstrated against vehicles from Tesla, BMW, Nissan, and Fiat Chrysler Automobiles (FCA).
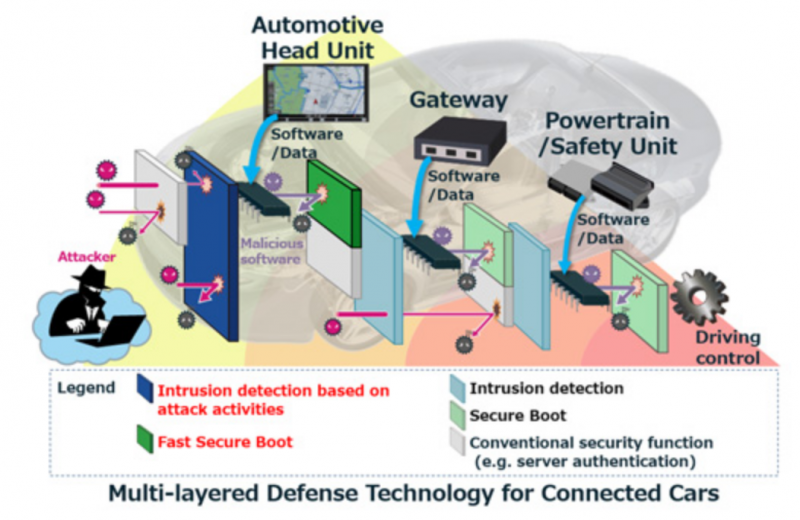
Mitsubishi has developed new technology that should protect connected cars against threats by using multiple layers of defense, including an intrusion detection system, secure booting, and authentication mechanisms.
The new defenses focus on protecting the automotive head unit, a component of the infotainment system and a car’s main link to the Internet, and systems responsible for controlling a vehicle.
According to Mitsubishi, the threat detection system focuses on typical attack-related activities in an effort to reduce load processing. The secure boot feature speeds up the booting process and ensures that the embedded software has not been tampered with by verifying its integrity.
The company says its new technology has been inspired by defenses originally developed for critical infrastructure systems, including ones used in the electric power, water, natural gas, and chemicals and petroleum sectors. However, that technology has been adapted for vehicles, where computing resources are more limited.
Related: Hackers Can Clone Tesla Key Fobs in Seconds
Related: New Vehicle Hack Exposes Users’ Private Data Via Bluetooth













