Researchers at cloud security firm RedLock believe hundreds of organizations may be exposing highly sensitive information by failing to properly configure Google Groups.
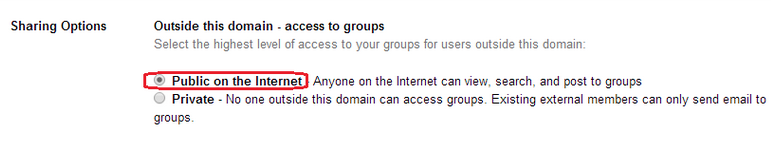
Google Groups is a service that allows users to create and take part in online forums and email-based groups. When a group is configured, its creator has to set sharing options for “Outside this domain – access to groups” to either “Private” or “Public on the Internet.”
RedLock’s Cloud Security Intelligence (CSI) team noticed that many Google Groups for Business users have allowed access to their groups from the Internet, and in some cases the configuration error has resulted in the exposure of sensitive information.
Researchers have found names, email and home addresses, employee salary data, sales pipeline data, and customer passwords in the exposed groups.
“We only looked for a sample of such cases and found dozens,” RedLock told SecurityWeek. “Extending that, there are likely hundreds of companies affected by this misconfiguration.”
According to RedLock, the list of affected firms includes IBM’s The Weather Company, which operates weather.com, intellicast.com and Weather Underground; Fusion Media Group, which owns Gizmodo, The Onion, Jezebel and Lifehacker; video ad platform SpotX, which delivers ads to 600 million people worldwide every month; and cloud-based helpdesk support provider Freshworks, whose software is used by more than 100,000 companies.
SpotX told SecurityWeek that it does set some Google Groups to public in order to collaborate with stakeholders outside the organization, but denied exposing any sensitive information.
Organizations using Google Groups have been advised to immediately check their settings to ensure that access is set to private in order to avoid leaking sensitive data.
“Simple misconfiguration errors – whether in SaaS applications or cloud infrastructure – can have potentially devastating effects,” said Varun Badhwar, CEO and co-founder of RedLock.
Badhwar pointed to the recent incidents involving Deep Root Analytics, WWE and Booz Allen Hamilton as examples of the impact such simple errors can have.
“This new issue that the RedLock CSI team discovered has led to the exposure of sensitive information from hundreds of companies simply through the click of a button,” Badhwar explained. “In today’s environment, it’s imperative that every organization take steps to educate employees on security best practices and leverage tools that can automate the process of securing applications, workloads and other systems. In the cloud, for example, a resource only exists for 127 minutes on average – there’s no way for IT teams alone to keep up with this rapid rate of change.”
*Updated with clarifications from SpotX
Related Reading: Configuration Error Embarrasses UK’s Cyber Essentials
Related Reading: Verizon Downplays Leak of Millions of Customer Records















