Microsoft reported this week that it has spotted Zerologon attacks apparently conducted by TA505, a notorious Russia-linked cybercrime group.
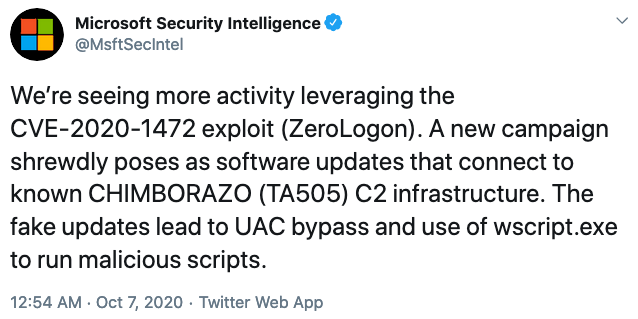
According to Microsoft, the Zerologon attacks it has observed involve fake software updates that connect to command and control (C&C) infrastructure known to be associated with TA505, which the company tracks as CHIMBORAZO.
The fake updates are designed to bypass the user account control (UAC) security feature in Windows and they abuse the Windows Script Host tool (wscript.exe) to execute malicious scripts.
“To exploit the vulnerability, attackers abuse MSBuild.exe to compile Mimikatz updated with built-in ZeroLogon functionality,” Microsoft said.
The tech giant added, “Attacks showing up in commodity malware like those used by the threat actor CHIMBORAZO indicate broader exploitation in the near term.”
TA505, also known as Evil Corp, has been active for nearly a decade and it’s mainly known for operations involving banking trojans and ransomware. This is not the first time the group has exploited Windows vulnerabilities in its attacks, and researchers recently found some links between campaigns conducted by TA505 and North Korean hackers.
Microsoft first warned users about malicious actors exploiting the Zerologon vulnerability on September 24. Earlier this week, it issued another warning after seeing that the flaw had also been exploited by an Iranian state-sponsored threat actor.
The Zerologon vulnerability, officially tracked as CVE-2020-1472 and described as a privilege escalation issue, affects Windows Server and it has been rated critical. It was patched by Microsoft in August with its monthly security updates.
The flaw allows an attacker who has access to the targeted organization’s network to compromise domain controllers without the need for credentials.
Microsoft has informed customers that applying the patches released in August is only the first phase of addressing the Zerologon vulnerability. The second phase, which will involve placing domain controllers in enforcement mode, will start in February 2021.
A few weeks after the vulnerability was fixed by Microsoft, the DHS issued an emergency directive requiring federal agencies to immediately install the available patches.
Related: CISA Warns of Hackers Exploiting Zerologon Vulnerability
Related: Samba Issues Patches for Zerologon Vulnerability
Related: Russia-Linked Cybercriminals Use Legitimate Tools in Attacks on German Firms

