Microsoft warned users on Thursday that it has spotted a sophisticated piece of Android ransomware that abuses notification services to display a ransom note.
Android ransomware typically allows cybercriminals to make a profit not by encrypting files — such as in the case of ransomware targeting desktop systems — but by displaying a full-screen ransom note that is difficult for the user to remove.
Microsoft says this particular Android ransomware family has been around for a while and its developers have continued to make improvements. Previous variants of the malware abused Android accessibility features or system alert windows to display the ransom note. However, Google has been taking steps to prevent abuse of these features, and some methods used by attackers can be easily spotted or bypassed by the victim.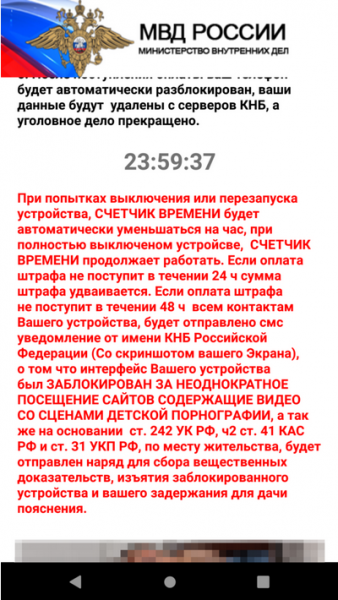
In an effort to increase its chances of success, the latest version of the Android ransomware, which Microsoft tracks as AndroidOS/MalLocker.B, uses a new technique to display the ransom note and make it more difficult to remove.
The ransomware note is usually a fake police notice informing the victim that explicit images had been found on their device and instructing them to pay a fine within 24 hours.
The malware displays the ransom note using a “call” notification, which requires immediate attention from the user, combined with the “onUserLeaveHint()” callback method of the Activity class, which is called when an application is about to go into the background after the user has pressed the home key on their smartphone.
“The malware overrides the onUserLeaveHint() callback function of Activity class. The function onUserLeaveHint() is called whenever the malware screen is pushed to background, causing the in-call Activity to be automatically brought to the foreground,” explained Microsoft researcher Dinesh Venkatesan.
This ensures that the ransom note continues to be displayed on the screen regardless of what the victim does.
Microsoft also noted that it spotted a piece of code in the latest version that leverages an open source machine learning module which allows developers to automatically resize and crop an image based on the size of the device’s screen.
This code does not appear to be used in current versions of the ransomware, but if it’s fully implemented, it will ensure that the ransom note is displayed on the screen without being distorted, which Microsoft says makes the threats more believable and increases the chances of the ransom being paid.
Microsoft has published a blog post with technical details on how the malware works and how organizations can protect themselves against such threats.
Related: Android Ransomware Asks for Victim’s Credit Card Info
Related: Android Ransomware Employs Advanced Evasion Techniques















