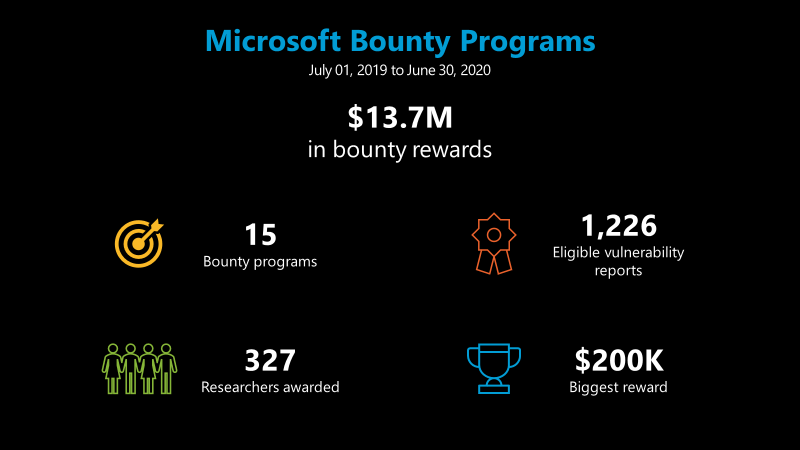
Microsoft reported on Tuesday that it paid out roughly $13.7 million through its bug bounty programs between July 1, 2019, and June 30, 2020.
The tech giant runs 15 bug bounty programs, which 327 researchers used in the past year to report 1,226 eligible vulnerabilities.
The single biggest reward paid out by the company was $200,000, with the highest rewards awarded for vulnerabilities in the Hyper-V hypervisor.
Researchers can earn up to $250,000 through the Hyper-V bounty program if they report a remote code execution vulnerability affecting the hypervisor and host kernel, but they must submit a high-quality report accompanied by a proof-of-concept with a functioning exploit.
Microsoft noted that the total amount paid out in the past year was over three times what it awarded researchers over the same period in the previous year ($4.4 million).
Between July 2019 and July 2020, Microsoft launched six new bug bounty programs and security initiatives, including Dynamics 365, Azure Security Lab, Edge on Chromium, Election Guard, Xbox and the Azure Sphere challenge. During the same period, it also announced updates to the Identity and Windows Insider Preview programs.
“In addition to the new bounty programs, COVID-19 social distancing appears to have had an impact on security researcher activity; across all 15 of our bounty programs we saw strong researcher engagement and higher report volume during the first several months of the pandemic,” Microsoft said in a blog post.
Related: Microsoft Open-Sources COVID-19 Threat Intelligence
Related: Microsoft Patches 123 Vulnerabilities With July 2020 Security Updates
Related: Microsoft Trials Election Security Solution in Wisconsin














