Blocking traffic from certain countries or regions might not be a very efficient way of defending against web attacks, according to an analysis conducted by web security firm Sucuri.
Sucuri has analyzed metadata from 30 days of traffic and more than 480 million requests blocked by its firewall product in order to collect information on the sources of web attacks and exploits. The study has focused on the browser, operating system and the country they come from.
Experts monitored not only the browser user agent, which can be easily spoofed, but also leveraged passive OS fingerprinting to obtain better results.
The SQL injection, brute force and other exploit attempts blocked by Sucuri over a 30-day period had various browser user agents. In 29 percent of cases, the attackers did not set a user agent, while in 16 percent of cases the agent was set to MSIE 6 (Internet Explorer 6), which is often faked by exploit tools. Chrome, GoogleBot and Firefox also made the top 5 – experts believe GoogleBot is likely used because it tricks webmasters into thinking that it’s a legitimate Google request.
WordPress, Java, BingBot, PHP and Perl also made the list, and while each of them account for less than one percent of the total, Sucuri believes they are still worth mentioning.
“Most of these happen when the exploit tool is not modified to change the user-agent or when it is using a specific platform as a middleman (in the case of WordPress). While they account for a small percentage overall, it does show how attackers could use out-of-the-box exploits,” explained Daniel Cid, founder and CTO of Sucuri.
When it comes to operating systems, the user agent showed that 45 percent of attacks came from Windows, five percent from Linux, four percent from Apple devices, while the rest did not specify an OS. However, OS fingerprinting and TCP analysis showed that most of the unidentified operating systems are likely Linux.
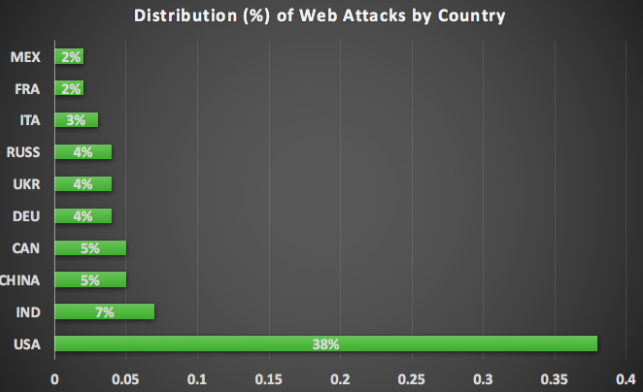
As for location, more than one-third of the attacks monitored by Sucuri came from the United States, followed by Indonesia, China, Canada, Germany, Ukraine and Russia. Researchers determined that California accounts for 11 percent of attacks.
“So, even though a partial geo-blocking may be effective as a noise reducer, it won’t really stop most attacks, unless you are willing to block the USA,” Cid explained.
“This data shows us that attacks are very diverse. You can’t just block attackers using one specific bit of data without looking at the complete picture,” the expert added. “Second, user-agents cannot be trusted and can be deceiving. Do not base decisions solely on that data.”
Related Reading: Thousands of CCTV Devices Abused for DDoS Attacks
Related Reading: DDoS Attacks Continue to Rise in Power and Sophistication
















