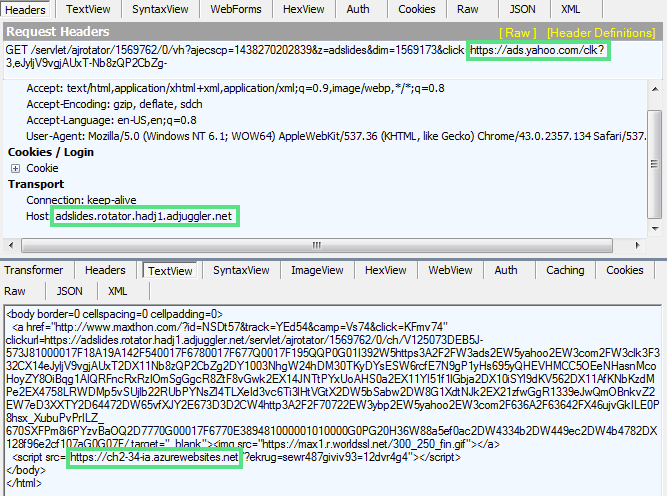
A large malvertising attack recently hit the Yahoo! advertising network, which leveraged Microsoft Azure websites and eventually redirected browsers to pages hosting the Angler Exploit Kit to compromise systems.
The malicious campaign started on July 28, and was shut down on Aug. 3, according to Malwarebytes, the security firm that discovered the attack.
“Many of the website’s 6.9 billion readers could have been affected, making this one of the largest malvertising attacks Malwarebytes Labs has seen recently,” Jerome Segura, senior security researcher at Malwarebytes Labs, wrote in a blog post.
Segura warned that victims of the attack were infected with ransomware via the Angler Exploit Kit, noting that it was also possible that banking trojans to other advertising fraud could have been used in the attack.
After notifying Yahoo! of the attack, Malwarebytes said the Internet firm responded quickly and took action to stop the campaign.
“Yahoo is committed to ensuring that both our advertisers and users have a safe and reliable experience,” Yahoo said in a statement. “As soon as we learned of this issue, our team took action and will continue to investigate this issue.”
The developers of the Angler Exploit Kit recently updated the crimeware to make it more difficult to track down the sources of a malvertising campaign. The exploit kit now breaks the referrer chain, which plays an important part when disrupting malvertising operations, security researcher Yonathan Klijnsma, told SecurityWeek in May.
According to data released today by security firm RiskIQ, in the first half of this year the number of malvertisements has jumped 260 percent compared to the same period in 2014.
“The sheer number of unique malvertisements has climbed 60 percent year over year. Meanwhile, fake Flash updates have replaced fake antivirus and fake Java updates as the most commonly method used to lure victims into installing various forms of malware including ransomware, spyware and adware,” RiskIQ said.
“Malvertising campaigns exploit a number of systemic weaknesses within the web’s ecosystem. These campaigns target verification and validation weaknesses in the ad networks and platforms,” Lane Thomas, Security Research and Software Development Engineer at Tripwire, told SecurityWeek. “Then, after successfully gaining access to these ad systems, the associated attackers take advantage of scale and lax patching. Scale is an issue here because one successful penetration of an ad system leads to huge payoff in terms of the total number of victims who can be attacked via malicious ads.”
“The final problem, which is where the exploit kit aspect of this problem wins, is due to massive amounts of lax software patching,” Thomas said. “Exploit kits focus largely on vulnerabilities in Adobe Flash, Java, and Silverlight along with vulnerabilities in the core web browsers themselves, and exploit kits thrive because so many end users don’t keep their software patched and updated.”















