Researchers from Seculert have discovered a new malware they dubbed “Magic”, due to “magic code” used within a custom communication protocol that the threat uses to communicate with its command and control servers.
The sample came to Seculert from a customer sometime during the past month, after it was uploaded to Seculert Swamp, the company’s cloud-based, automated malware analysis service.
According to Seculert, the sample was flagged because its behavior seemed out of the ordinary for a legitimate executable.
“Usually, when a malware initiates a communication with a C2 server, the first response is a setting, telling the malware what to do next,” Aviv Raff, CTO of Seculert, explained in a blog post.
In this case, the C2 (Command and Control) server instructed the malware to start communicating with the same IP address and port, Raff said.
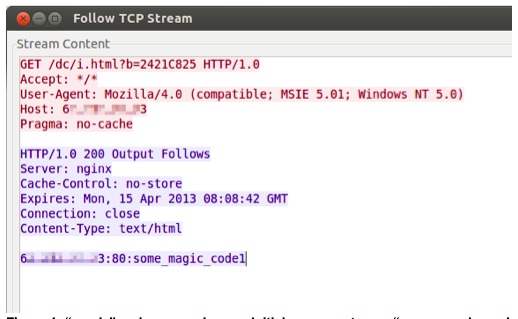
But from then on, Raff continued, instead of using the HTTP protocol commonly used by malware, “Magic” communicated with its C2 server using a custom-made protocol, always using a magic code at the beginning of the conversation as seen in the screenshot below.
In one case, as shown in the figure below, the malware asks for instructions from the C2 server.
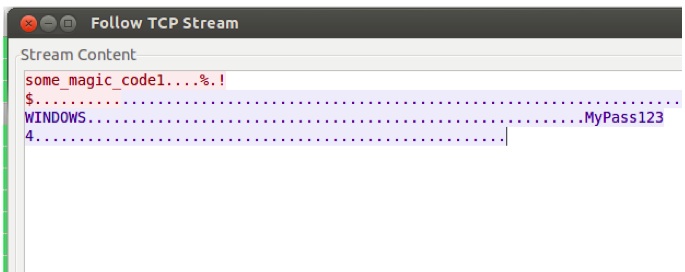
“The C2 server responds with a command to add a new backdoor user — Username: WINDOWS, Password: MyPass1234 — which enables the attacker to remotely access the infected machine or network,” Raff noted.
The Command and Control servers are located in France, Germany and the Netherlands, Raff told SecurityWeek.
Raff said that Magic is a fully functional custom-made RAT, with features that are still under development.
The attacks are currently active, and had remained undetected on the targeted machines for the past 11 months, Seculert said. Attackers have targeted several thousand entities, most of them located in the United Kingdom, with several different industries being targeted, including Finance, Education and Telecom.
Seculert said they have seen other variants of the malware that date back to May 2012, though the malware appears to still be under development by the attackers.
“For instance, in case the attacker would like to open a browser on the victim’s machine, the malware will popup on the RDP session for the attacker a box with the message: ‘TODO:Start browser!’” Raff explained.
Seculert is currently investigating the infection vector, though they did say that the malware is being downloaded by another malware.
The malware authors are using English in the code, but Raff suspects they are probably not native English speakers.
While the true intentions of the attackers behind the malware are not certain, the goal appears to be to stealing information, and Seculert believes that the current phase of the attack is to monitor the activities of their targeted entities.
“Because this malware is also capable of downloading and executing additional malicious files, this might be only the first phase of a much broader attack,” Raff opined.
“We have yet to find any indication that this is a state-sponsored attack,” he said.
















