Flashback Trojan Attempts to Disable Apple’s XProtect
A Trojan targeting Mac OS X, named Flashback by some vendors, is disabling the XProtect component of Apple’s operating system. The latest research on the malware samples collected by F-Secure offer some interesting comparisons to Windows-based Trojans.
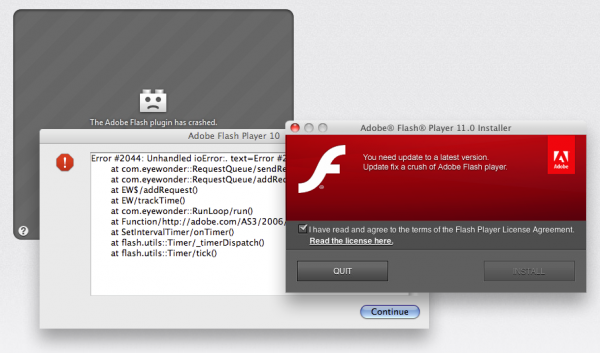
Flashback is a Trojan that targets Mac OS X installations. The name comes from the fact that it presents itself as an update to Adobe Flash, or Flash Player installer. Once installed, the malware will check for Little Snitch, OS X’s firewall. If detected, it will delete itself, otherwise if the firewall isn’t found; it will install and wait for additional payloads from a remote host.
Windows users are used to seeing malware disguised as legitimate software, and it appears that criminals are betting the same tricks will work on Mac users when it comes to increasing their victim counts. In addition to the firewall check, Flashback will also search for VM instances. If Flashback finds itself in a virtual environment, this too will trigger a self-removal routine.
“VMware-aware malware is a common anti-research technique used within the Windows ecosystem, but not yet so in Mac’s. It appears that Mac malware authors are anticipating that researchers will begin to use virtualized environments during analysis, and are taking steps to hamper such efforts,” an F-Secure researcher noted.
The latest research on a third variant of the OS X malware includes another feature often seen in Windows infections, anti-security measures. In this case, Flashback targets XProtect, Apple’s anti-malware application embedded within OS X. Once installed successfully, Flashback will disable XProtect’s automatic update features, preventing new detections from being installed to the infected host.
“Attempting to disable system defenses is a very common tactic for malware – and built-in defenses are naturally going to be the first target on any computing platform,” the researcher added.
There are three variants of Flashback. According to F-Secure, two of them cannot connect to their remote hosts, as they are offline. The third can connect to the remote host for additional payloads, but the host isn’t serving anything. Also, unlike the first version, the other variants are requiring an administrator password before proceeding with installation.