Two researchers in Israel, Yair Amit and Adi Sharabani, recently disclosed that LinkedIn’s mobile application for iOS was transmitting calendar information back to the business social network, without the user being aware in most cases.
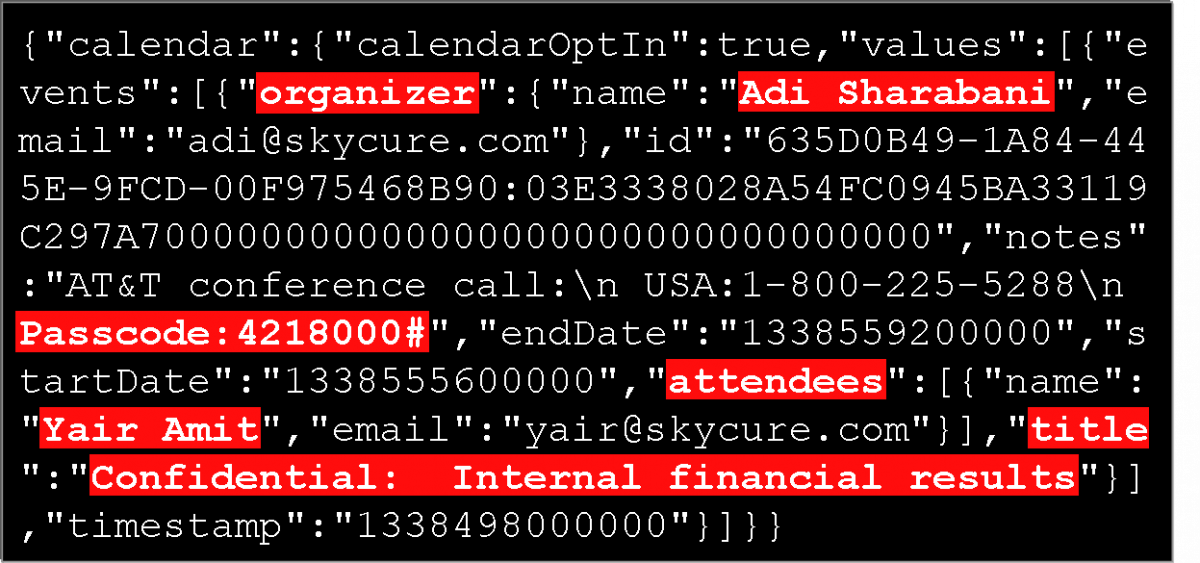
The feature is opt-in, and it allows LinkedIn subscribers to view their iOS calendar information via the site’s mobile app. Once users agree, the mobile app will transmit calendar information, including meeting locations, participant information, dial-in details (numbers and passcodes), and meeting notes back to LinkedIn’s servers. Both personal and corporate calendars are included in the data collection.
According to their research, each time a user launches LinkedIn’s app on a connected iOS device, it automatically sends out all of your calendar entries for a five-days time frame. “This applies to all calendars configured in the iOS machine, whether they are associated with your private email account or the corporate Exchange account,” Sharabani, who serves as CEO of Skycure Security explained.
“As I said before, in some cases, grabbing users’ sensitive data might be okay. It is never right to do so without a clear indication,” Adi said. “It is far worse when the sensitive information is not really needed in the first place.”
When confronted with the research, LinkedIn told The New York Times that they use the collected information “to match LinkedIn profile information about who you’re meeting with so you have more information about that person.”
However, is there is a way to opt-out of the data collection. The steps below will work for the iPhone version of the app, as well as the iPad version.
1. Click on the LinkedIn icon in the upper left part of the screen
2. Click on the “You” view
3. Click on the settings icon in the upper right part of the screen
4. Click on the “Add Calendar” option in the Settings page
5. Toggle off the “Add Your Calendar” option.
LinkedIn has not yet commented on what happens to the information once it is collected and determined that it isn’t relevant, such as storage and removal policies. The researchers reported the problems to LinkedIn’s risk and privacy team, but as of Tuesday evening, they remained unchanged, likely do to the fact that the social portal for the corporate world sees the data collection as a feature, and not a true concern.
Sharabani will be presenting his findings at a Cyber Security conference in taking place at Tel Aviv University later today.

