A ransomware group has leaked files showing the extent of their access to Western Digital systems and it appears that the hackers were closely monitoring the company’s initial response to the breach from within its network.
The digital storage giant announced a service outage on April 2 and the next day it confirmed that the cause was a cyberattack. The company at the time admitted that the hackers had gained access to some data, but it did not share any details.
The company has not provided any updates on the incident since its initial statement one month ago.
However, the ransomware group known as Alphv/BlackCat has taken credit for the attack and they recently published dozens of screenshots showing the extent of their access.
The screenshots include what appear to be video calls, emails and internal documents discussing the hack, as well as invoices, development tools, confidential communications, and various tools used internally by the company.
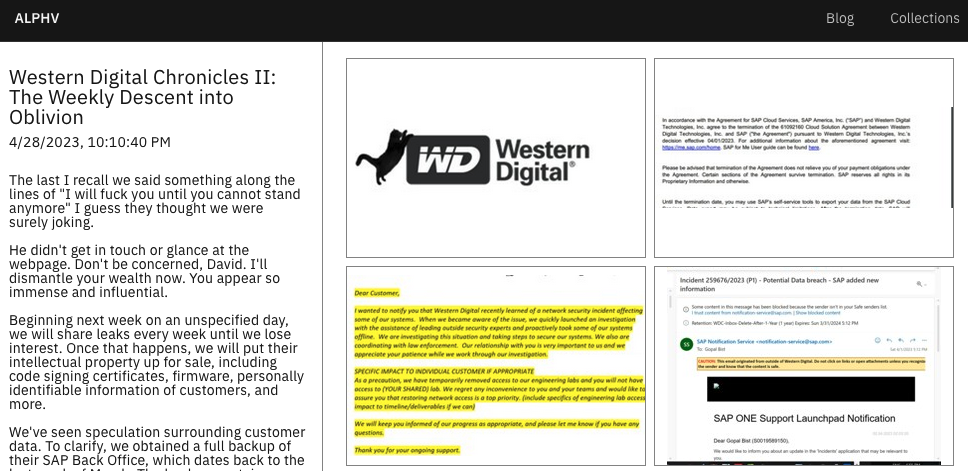
The screenshots suggest that the hackers had access to WD systems until at least April 1.
The hackers said that, unless WD pays up, they will release stolen files every week. They also threaten to sell stolen intellectual property, including firmware, code signing certificates, and customer personal information.
The BlackCat/Alphv group recently also took credit for an attack on US payments giant NCR.
Related: Microsoft: Cl0p Ransomware Exploited PaperCut Vulnerabilities Since April 13
Related: Capita Confirms Data Breach After Ransomware Group Offers to Sell Stolen Information
Related: Ransomware Attack Hits Health Insurer Point32Health

