Kognos emerged from stealth mode on Tuesday with an extended detection and response (XDR) platform that the company says leverages artificial intelligence to enable organizations to more efficiently detect, investigate and respond to attacks.
Kognos’ platform, named Autonomous XDR Investigator, is described as a relationship-centric XDR platform that should significantly simplify investigations into attacker behavior and operations.
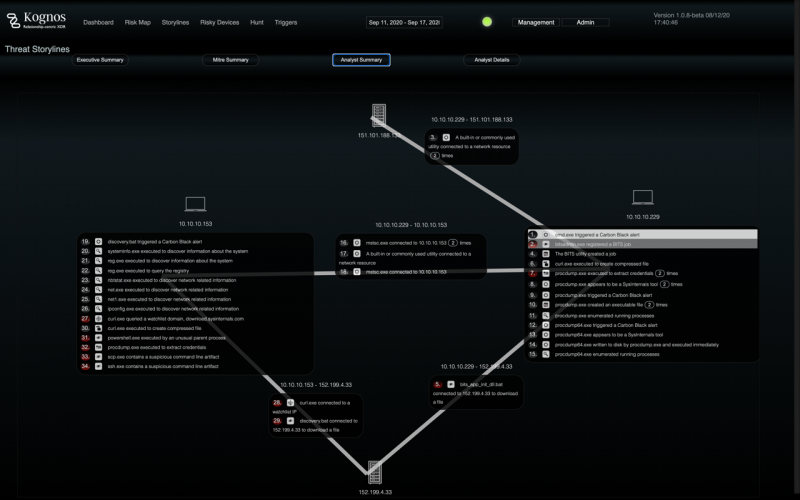
The platform generates relationship graphs using data from the organization’s existing solutions, including endpoint detection and response (EDR), network detection and response (NDR), and security information and event management (SIEM) products.
These relationship graphs are analyzed by Kognos’ inquiry engine in an effort to find information on the attacker’s activities. This information is then fed to the platform’s “story generation engine,” which generates a timeline of the attack, enabling a quick response from the security team.
The company claims its platform can help reduce the time needed to investigate malicious activity by automating alert triage, it can help track an attacker’s movement within the network (including their use of living-off-the-land methods), and help identify insider threats.
The platform can be integrated with products from many vendors, including VMware, Crowdstrike, Splunk, RSA, Elastic, AWS, Microsoft (Azure), VirusTotal, and Team Cymru, as well as several free and open source tools.
The company told SecurityWeek that it plans on extending the platform to support additional integrations, and extending the curated Q&A based on new integrations.
One of Kognos’ founders is Rakesh Nair, former head of engineering at Netwitness/RSA, who will serve as the company’s CEO.
“Today’s threat actor lives and thrives within enterprise environments with the ability to freely execute lateral campaigns, live off the environment itself, or offer a prime opportunity for insider threats to siphon information for financial gain,” Nair said. “With Kognos, enterprises can now gain real-time visibility of all of these scenarios as they are happening and act immediately to prevent the ability for attackers to fully execute campaigns.”
Kognos told SecurityWeek that it has raised $1.8 million to date, from Lucas Venture Group, Cyber Mentor Fund and angel investors.
Related: Palo Alto Networks to Acquire Incident Response Firm The Crypsis Group for $265 Million
Related: Data Security Company Symmetry Systems Emerges From Stealth
Related: Adaptive Shield Emerges From Stealth to Secure SaaS Applications