Kaspersky Download Web Site Gets Hacked
Even reputable security providers fall victim to cyber attacks. Over the weekend, anti-virus software maker Kaspersky Lab, experienced an attack in which a third party application on the company’s servers was exploited in order to redirect a would-be downloader of Kaspersky’s anti-virus software, to download fake anti-virus malware.
Many users flocked to the Kaspersky Lab forums to discuss the various warning messages they received about possible malware when trying to download Kaspersky’s legit anti-virus software.
We contacted Kaspersky for comment, but the company was unable to provide details beyond a standard response, due to the fact that an investigation was in progress surrounding the incident.
The company, with its global headquarters in Moscow and US headquarters in Woburn, MA issued the following statement:
Kaspersky Lab reports that at 11:05 PM GMT on Sunday, October 17, 2010 the kasperskyusa.com domain experienced a hacker attack that exploited a vulnerability on a third party application.
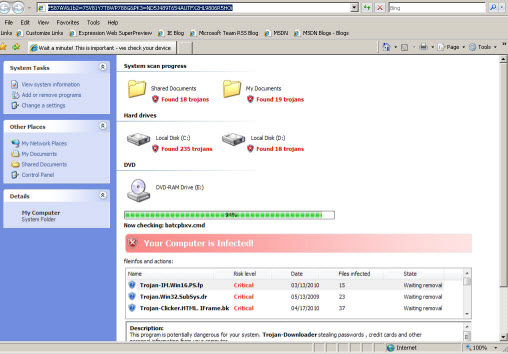
As a result of the attack, users trying to download Kaspersky Lab’s consumer products were redirected to a malicious website. The website was simulating a Windows XP Explorer window and a popup window showing scanning process on the local computer and offering the user a fake antivirus program to install. The domain was making these redirections for 3.5 hours in total.
Upon being notified about the vulnerability, company personnel took immediate action to address the issue, and the affected server was taken offline within 10 minutes. Immediately following, all vulnerable components were removed from the server and clean files were restored from the central repository. A complete audit of the kasperskyusa.com domain, as well as all of the other Kaspersky Lab domains, was done to ensure they’re running fully updated code. Currently the server is secure and fully back online, and Kaspersky products are available for download.
Kaspersky Lab also wants to confirm that no individual’s details were compromised from the company’s web servers during this attack. However, Kaspersky Lab takes any attempt to compromise its security seriously. Our researchers are currently working on identifying any possible consequences of the attack for affected users, and are available to provide help to remove the fake antivirus software.
Related Reading: An Inside Look at Hacker Business Models
















