A group of Iranian hackers recently posted a video showing how they managed to access an industrial control system (ICS) at a water facility in Israel.
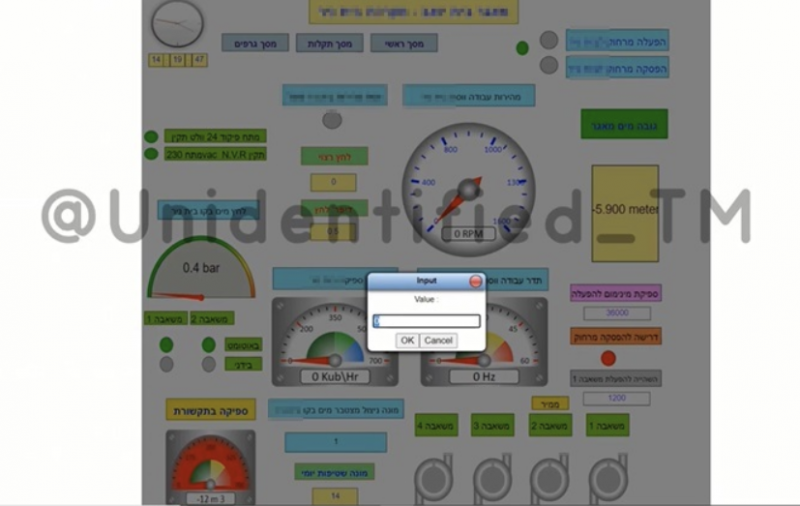
According to industrial cybersecurity firm OTORIO, the hackers accessed a human-machine interface (HMI) system that was directly connected to the internet without any authentication or other type of protection. The target was apparently a reclaimed water reservoir.
“This gave the attackers easy access to the system and the ability to modify any value in the system, allowing them, for example, to tamper with the water pressure, change the temperature and more. All the adversaries needed was a connection to the world-wide-web, and a web browser,” OTORIO said in a blog post.
The hackers published their video on December 1 and by the next day the owner of the compromised system made some changes to prevent access to the HMI without authentication. However, OTORIO researchers noticed that the system itself is still exposed to the internet, allowing more skilled attackers to access it.
Cybersecurity professionals have long warned that malicious actors could cause serious damage to organizations in the energy and water sectors by targeting exposed HMIs.
OTORIO told SecurityWeek that the target is a relatively small site with a capacity of roughly 4-6 million cubic meters.
The company’s researchers could not say for sure what type of damage the attackers could have caused but said the “damage potential is very high.”
“Often there are other safety mechanisms (some mechanical) that can reduce the damage, but if such a system is not in place, the consequences can be catastrophic,” Noam Even, threat intelligence researcher at OTORIO, told SecurityWeek.
The Iranian hacker group that targeted this water facility in Israel is called the “Unidentified TEAM” and it does not appear to possess deep capabilities or knowledge for targeting industrial systems.
Learn more about threats to industrial systems at SecurityWeek’s ICS Cyber Security Conference and SecurityWeek’s Security Summits virtual event series
The same group recently also targeted a governmental education website in Texas, which the hackers claimed was in response to the killing of Mohsen Fakhrizadeh, a top Iranian nuclear scientist. Both Iranian and US officials reportedly said Israel was behind the assassination.
This is not the first time Iranian hackers have targeted Israel’s water sector. There were at least two rounds of attacks this year, mainly targeting smaller, local facilities. Authorities said the attacks did not cause any damage, but the attackers apparently knew how to target industrial systems.
OTORIO’s Even told SecurityWeek that Israel’s water and water treatment facilities are generally secure, but noted that private facilities such as the one targeted earlier this month are “very loosely regulated and can be an easy target for attackers.”
Related: Hackers Knew How to Target PLCs in Israel Water Facility Attacks
Related: Vulnerable Cellular Routers Targeted in Latest Attacks on Israel Water Facilities
Related: Israeli Cyber Chief: Major Attack on Water Systems Thwarted
Related: Israel Says Foiled Cyber Attack on Its Defence Firms















