A threat group said to be associated with Iranian government-directed cyber operations is believed to be operating a fake online persona to target organizations in the Middle East with malware, SecureWorks researchers say.
Known as COBALT GYPSY or TG-2889, the threat group was previously associated with various campaigns, including Shamoon attacks, which were apparently orchestrated by multiple groups working together.
Phishing campaigns observed in early 2017 and aimed at entities in the Middle East and North Africa (MENA), with a focus on Saudi Arabian organizations, used the PupyRAT open-source remote access Trojan have also been associated with the COBALT GYPSY, SecureWorks says.
These likely unsuccessful campaigns were followed by “highly targeted spearphishing and social engineering attacks” from an entity using the online persona Mia Ash. SecureWorks believes that COBALT GYPSY was behind these attacks as well, and the threat group used spearphishing to target telecommunications, government, defense, oil, and financial services organizations in the MENA region.
“Further analysis revealed a well-established collection of fake social media profiles that appear intended to build trust and rapport with potential victims. The connections associated with these profiles indicate the threat actor began using the persona to target organizations in April 2016,” the researchers say.
The phishing campaigns observed at the end of 2016 used shortened URLs leading to a macro-enabled Word document that executed a PowerShell command to download additional PowerShell loader scripts for PupyRAT. Successful installation of the malicious program would have provided the attackers with full access to the victims’ systems.
In January, an employee at one of the targeted organizations was contacted via LinkedIn by a purported London-based photographer named Mia Ash, who claimed to be reaching out as part of a worldwide exercise. Following multiple messages about professions, photography, and travels, Mia Ash eventually encouraged the employee to become friends on Facebook and continue the conversation there.
After communicating for several weeks via email, WhatsApp, and likely Facebook, Mia Ash eventually sent a Microsoft Excel document titled “Copy of Photography Survey.xlsm” and encouraged the employee to open “the email at work using their corporate email account so the survey would function properly.” Macros included in the document downloaded the PupyRAT malware.
SecureWorks believes COBALT GYPSY is behind the Mia Ash persona, using it to infect the targeted organizations after the initial campaigns failed. “The group has repeatedly used social media, particularly LinkedIn, to identify and interact with employees at targeted organizations, and then used weaponized Excel documents to deliver RATs such as PupyRAT,” the researchers note.
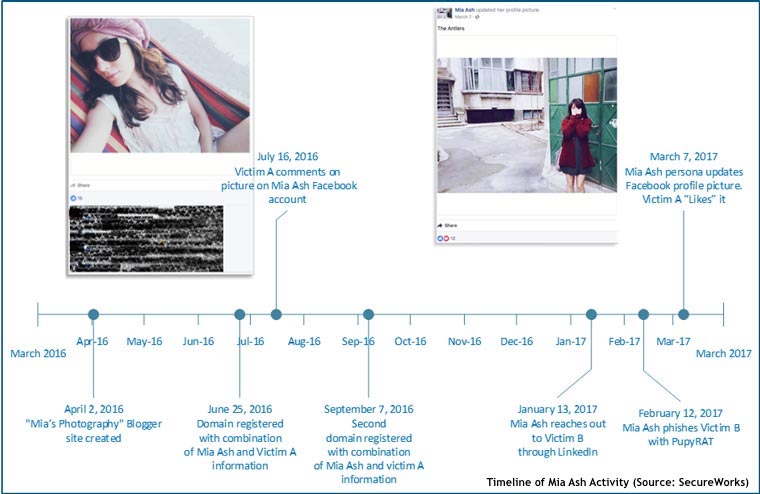
Mia Ash, the researchers say, is highly likely fake, although associated with LinkedIn, Facebook, Blogger, and WhatsApp accounts, and several email addresses. The persona appears to have been established in April 2016 or earlier, while the accounts appear to feature supporting material and content originating from other sources.
The LinkedIn profile contains a description of employment at Mia’s Photography seemingly taken from the LinkedIn page of a U.S.-based photographer. The images used by Mia Ash, consistent across the various accounts and profiles, were likely taken from the social media accounts belonging to a Romanian photographer.
The researchers also observed that several of Mia Ash’s LinkedIn connections match the names of people associated with the Mia Ash Facebook page, suggesting that the threat actor is initially contacting individuals on LinkedIn, then switching to Facebook. Photography connections were used to project authenticity, but multiple non-photography endorsers located in Saudi Arabia, United States, Iraq, Iran, Israel, India, and Bangladesh appear to be targets working for technology, oil/gas, healthcare, aerospace, and consulting organizations.
These individuals had job titles such as technical support engineer, software developer, and system support, implying elevated access within the corporate network. Threat actors are looking to compromise accounts with admin or elevated access to “quickly access a targeted environment to achieve their objectives.”
“The individuals’ locations and industries align with previous COBALT GYPSY targeting and Iranian ideological, political, and military intelligence objectives. These characteristics suggest that COBALT GYPSY executed the January and February phishing campaigns and that it created the Mia Ash persona,” SecureWorks says.
The security researchers have been tracking multiple COBALT GYPSY campaigns since 2015 and say it is highly likely that the group is connected to Iranian government-directed cyber operations, given that it has launched espionage campaigns against organizations “of strategic, political, or economic importance to Iranian interests.”
According to SecureWorks, the threat group might have created multiple online personae to gain access to targeted computer networks via social engineering. “The use of the Mia Ash persona demonstrates the creativity and persistence that threat actors employ to compromise targets. The persistent use of social media to identify and manipulate victims indicates that COBALT GYPSY successfully achieves its objectives using this tactic,” the researchers conclude.
Related: Iranian Cyberspy Groups Share Malware Code
Related: Multiple Groups Cooperated in Shamoon Attacks: Symantec
Related: Iranian Spies Target Saudi Arabia in “Magic Hound” Attacks
















