Researchers Warn DDS Protocol Can Be Abused for Lateral Movement and Malware C&C
Researchers have shown that a widely used protocol named Data Distribution Service (DDS) is affected by vulnerabilities that could be exploited by threat actors for various purposes.
Maintained by the standards development organization Object Management Group (OMG), DDS is a middleware protocol and API standard for data connectivity that is advertised as ideal for business-critical IoT systems. DDS has been used in sectors such as public transportation, air traffic management, aerospace, autonomous driving, industrial robotics, medical devices, and missile and other military systems.
DDS has been used by organizations such as NASA, Siemens, and Volkswagen, as well as in the popular Robot Operating System (ROS).
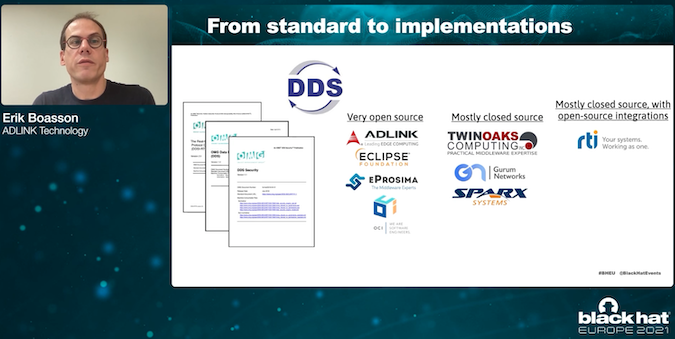
There are both open source and closed source implementations of DDS, including by ADLINK Technology, Eclipse (CycloneDDS), eProsima (Fast DDS), OCI (OpenDDS), TwinOaks Computing (CoreDX DDS), Gurum Networks (GurumDDS), and RTI (Connext DDS).
Researchers from Trend Micro, TXOne Networks, Alias Robotics, and ADLINK Technology have analyzed the DDS standard and the aforementioned implementations and discovered a total of more than a dozen vulnerabilities.
The researchers disclosed some of their findings at the Black Hat Europe 2021 cybersecurity conference last week, with a research paper detailing their work being planned for early next year.
In the meantime, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) has released an industrial control systems (ICS) advisory related to the research.
“CISA is issuing this advisory to provide early notice of the reported vulnerabilities and identify baseline mitigations for reducing risks to these and other cybersecurity attacks,” CISA said.
According to CISA, patches have been released for CycloneDDS, FastDDS, OpenDDS, Connext DDS, and CoreDX DDS. There do not appear to be any patches from Gurum, which the researchers said ignored several notification attempts.
Identified vulnerabilities include write-what-where condition, improper handling of invalid structure, network amplification, buffer allocation, and buffer overflow issues.
The flaws can be exploited by threat actors for arbitrary code execution, obtaining information, or causing a denial of service (DoS) condition.
However, the researchers noted in their presentation at Black Hat that since DDS is typically deployed locally and deep in the control network, it’s unlikely that attackers would find internet-exposed systems.
On the other hand, they pointed out that DDS could still be abused by an attacker who already has access to the targeted entity’s systems for the discovery of other endpoints, lateral movement, and for malware command and control (C&C).
The researchers noted that the DDS codebase is large and complex and this research only scratches the surface.
Related: Vulnerabilities in OpENer Stack Expose Industrial Devices to Attacks
Related: Industrial Firms Informed About Serious Vulnerabilities in Matrikon OPC Product
Related: Vulnerabilities in Protocol Gateways Can Facilitate Attacks on Industrial Systems














