This year’s mobile-focused Pwn2Own hacking competition organized by Trend Micro’s Zero Day Initiative (ZDI) will include a new category for Internet of Things (IoT) devices.
The event, whose name has been changed from Mobile Pwn2Own to Pwn2Own Tokyo as a result of the expansion, will take place alongside the PacSec security conference in Tokyo, Japan, on November 13 – 14.
Hackers can earn over $500,000 in cash and prizes if they manage to find and exploit vulnerabilities in devices from Google, Apple, Samsung, Huawei, Xiaomi, Amazon and Nest.
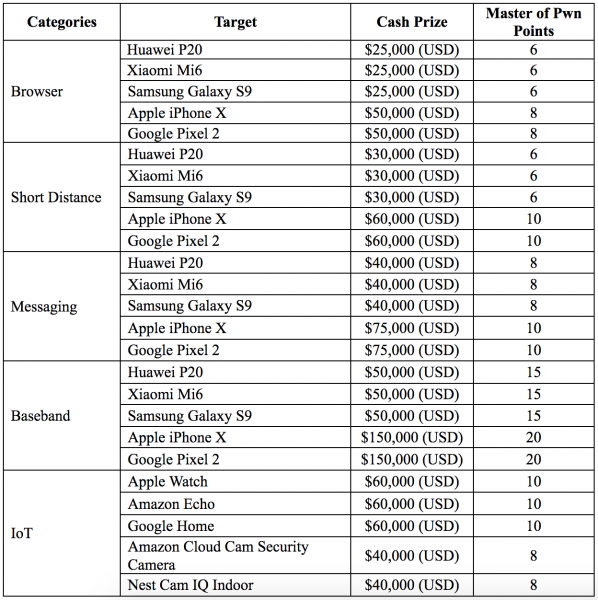
In the new IoT category, contestants can earn up to $60,000 if they can execute arbitrary code without user interaction on Apple Watch Series 3, Amazon Echo (2nd generation), Google Home, Nest Cam IQ Indoor and Amazon Cloud Cam devices.
In the web browsers category, security experts can receive a cash prize of $25,000 for hacking the default browser on Huawei P20, Xiaomi Mi6, and Samsung Galaxy S9, and $50,000 for a successful exploit against the browsers running on Apple’s iPhone X, and Google’s Pixel 2.
In the short distance category, which includes Wi-Fi, Bluetooth, and near field communication (NFC), ZDI is offering up to $30,000 and up to $60,000 – exploits targeting devices from Apple and Google are worth the higher amount.
Hacking a device simply by sending it a SMS/MMS message or getting its owner to view a message can earn Pwn2Own Tokyo contestants as much as $75,000.
The highest rewards are offered this year for baseband attacks, which involve the target device communicating with a rogue base station. Researchers can get up to $50,000 for a successful exploit against Huawei, Xiaomi and Samsung devices, and up to $150,000 for hacking Apple and Google phones.
In the browser and short-range categories, participants can earn an extra $20,000 if their exploit payload is executed with kernel privileges. There is also a persistence bonus for these categories: $50,000 if the exploit survives a reboot on an iPhone X, and $25,000 if it survives a reboot on a Pixel 2.
Registration for Pwn2Own Tokyo closes on November 7 at 5:00 p.m. Japan Standard Time.
At last year’s event, hackers earned more than half a million dollars after successfully demonstrating exploits against the Samsung Galaxy S8, the Apple iPhone 7 and the Huawei Mate 9 Pro. No attempts were made against the Google Pixel.














