Organizations have been warned that hackers are scanning the internet for vulnerable Microsoft Exchange servers affected by a series of vulnerabilities that were disclosed by researchers last week.
Orange Tsai, principal researcher at security consulting firm DEVCORE, discovered that Microsoft Exchange servers are affected by three vulnerabilities that can be exploited by unauthenticated attackers for remote code execution.
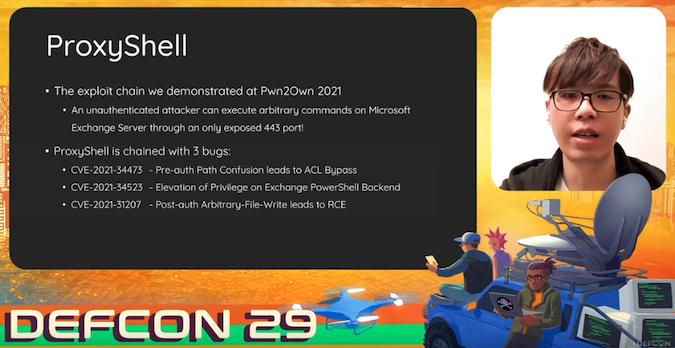
The flaws have been assigned the CVE identifiers CVE-2021-34473, CVE-2021-34523 and CVE-2021-31207, and they are collectively tracked as ProxyShell.
Orange Tsai has been looking for vulnerabilities in Microsoft Exchange Server since October 2020, and he also informed Microsoft about the flaws tracked as ProxyLogon, which ended up being widely exploited by both profit-driven cybercriminals and state-sponsored threat actors.
The researcher said Microsoft released patches for the ProxyShell vulnerabilities in mid-April. However, the tech giant only published advisories for the flaws in May and July.
Microsoft described them as a medium-severity security feature bypass, a critical privilege escalation, and a critical remote code execution issue. Only one bug, CVE-2021-34473, was assigned an “exploitation more likely” rating by Microsoft.
The DEVCORE team used the ProxyShell exploit at the 2021 Pwn2Own hacking contest to take control of an Exchange server, which earned them a $200,000 bug bounty. However, details of the exploit were privately reported at the time to the vendor and were not made public.
Orange Tsai presented the technical details of ProxyShell and other Exchange vulnerabilities at the Black Hat and DEF CON cybersecurity conferences last week. Following the presentations, other researchers published a blog post detailing the vulnerabilities.
Shortly after, researcher Kevin Beaumont reported that one of his honeypots recorded attack attempts involving the ProxyShell exploit. “My Exchange honeypot has somebody dropping files and executing commands,” he said on Twitter on Saturday.
Beaumont and others have released indicators of compromise (IOCs) for these exploitation attempts. National cybersecurity agencies in Europe started issuing alerts in response to the reports.
While patches have been available for months, there appear to be many Microsoft Exchange servers that are still vulnerable to ProxyShell attacks, so it would not be surprising if multiple threat actors started exploiting the flaws in their operations.
Related: U.S., Allies Officially Accuse China of Microsoft Exchange Attacks
Related: CISA Details Malware Found on Hacked Exchange Servers
Related: Over 80,000 Exchange Servers Still Affected by Actively Exploited Vulnerabilities














