The energy and utilities sector has seen an increasing number of cybersecurity incidents and attacks, according to a new IBM X-Force report published on Wednesday.
IBM reported late last year that the number of attacks aimed at industrial control systems (ICS) had increased by 110 percent in 2016. Data from IBM Managed Security Services for the first half of 2017 shows that more than 2,500 attacks have already been detected against the company’s customers, compared to 2,788 attacks identified in the entire last year.
When it comes to the energy and utilities industry, IBM says this sector has fallen just shy of the top 5 most targeted sectors in the first half of 2017. Last year, the company detected more than 39 million security events, 382 attacks, and 66 security incidents that were deemed worthy of further investigation.
Of all the attacks observed by IBM, 60 percent of unintentional and malicious attacks came from outside the organization, and the rest were caused by insiders. Insiders include both malicious actors (16%) and employees who unknowingly opened malicious files (24%), giving attackers remote access to the organization.
“In one publicly disclosed incident, thousands of files were stolen over an eight-month period from an infected computer at a Japanese university’s nuclear research lab Reportedly an employee opened a malicious email that caused the system to become infected and remotely accessible,” IBM said in its report. “The recent targeting of nuclear facilities in the US also involved spear-phishing, malicious Microsoft Word documents and a watering-hole attack.”
Related: Learn More at SecurityWeek’s 2017 ICS Cyber Security Conference
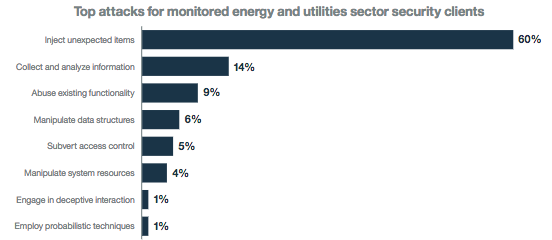
Sixty percent of the 2016 attacks against this sector involved some sort of injection method, including OS command injections (29%) and SQL injections (17%). In comparison, injection-type attacks accounted for only 42 percent of incidents across all the other industries monitored by IBM.
Other attacks involved information harvesting and analysis, abuse of existing functionality, and data structure manipulation.
Energy facilities in the United States and Europe have been increasingly targeted by sophisticated threat actors. While there is no evidence that the attacks caused any service disruptions, Symantec warned on Wednesday that a Russia-linked group known as Dragonfly, Crouching Yeti and Energetic Bear may have gained access to control systems, which could allow it to cause power outages in the future.
Related: Targeted Attacks on Industrial Sector Increasingly Common













