Secure remote access is essential for industrial organizations, but many employees who took part in a recent survey expressed concerns about the associated risks.
Cyolo, a firm that provides zero trust identity-based access solutions for IT and OT systems, on Wednesday published a new report titled ‘The State of Industrial Secure Remote Access’.
The report is based on a survey of more than 200 cybersecurity, IT and engineering professionals conducted by Takepoint Research in the first quarter of 2023. The respondents represented organizations of all sizes from North America, Europe and other regions around the world.
The survey found that industrial secure remote access (I-SRA) is important for many organizations, particularly for allowing third party access (cited by 72% of respondents), increasing productivity (68%), collecting data (51%) and reducing costs (41%).
The study showed some differences between industries. In the oil and gas industry, for instance, 83% of organizations need I-SRA for third party access and only 48% need it for data collection. In the manufacturing sector, however, remote access is needed for data collection in 72% of cases.
“Such differences include each organization’s business context, as well as various industrial, regional, and company-specific factors. Factors that influence operations include regulations, labor availability/cost, and the utilization of operational data for productivity and safety enhancement,” Cyolo explained in its report.
The number of users connecting remotely to an industrial organization’s systems largely depends on its size. But regardless of their size and number of connections, the survey found that all organizations are highly concerned about the risks associated with remote access.
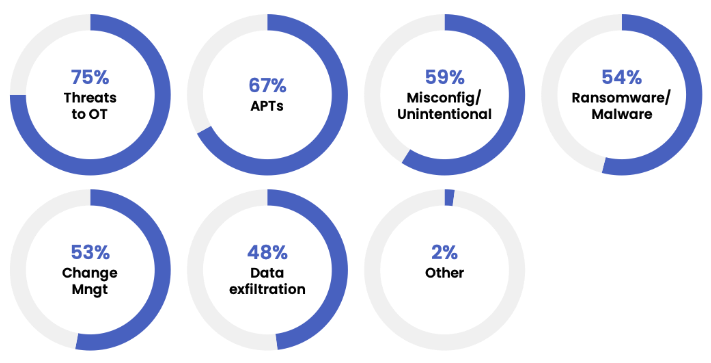
When asked about the biggest risks, three-quarter of respondents named threats to operational technology (OT), followed by APTs, misconfigurations, and malware.
The data shows that across all industries the level of confidence respondents had in their current I-SRA solutions is lower than the level of concern.
“Industrial settings have built brittle workarounds for securing remote access, like firewalls and Virtual Private Network (VPNs), and have sought to implement frameworks like NIST 800-82 or ISA/IEC62443. Still, they recognize that the problem is not solved,” Cyolo explained. “Simply put, teams allow remote access to their critical systems because operations depend on it – but that access is far less secure than they’d like.”
The organizations that took part in the study mainly want to secure remote access to reduce risk to operations safety and prevent cyber incidents. In the case of mid-size organizations (with 5k-10k employees), an important objective is to lower costs.
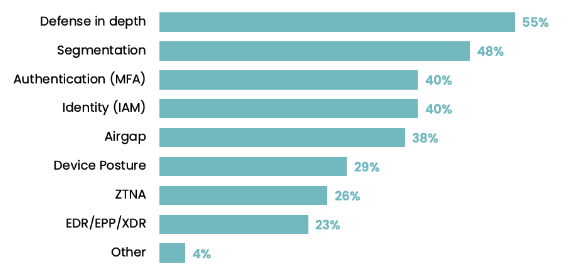
In order to minimize risks, industrial companies said they are already implementing defense-in-depth measures, using segmentation, improving authentication and IAM, as well as air-gapping critical systems.
However, they still have concerns, including the lack of visibility, user education, access control, and outdated operating systems.
The full report contains a breakdown of some of this data based on organization size and industry.
Learn More at SecurityWeek’s ICS Cyber Security Conference
The leading global conference series for Operations, Control Systems and OT/IT Security professionals to connect on SCADA, DCS PLC and field controller cybersecurity.
October 23-26, 2023 | Atlanta
www.icscybersecurityconference.com
Related: Teltonika Vulnerabilities Could Expose Thousands of Industrial Organizations to Remote Attacks
Related: Access to Energy Sector ICS/OT Systems Offered on Hacker Forums

