Researchers from industrial cybersecurity firm Claroty and developer security company Snyk have analyzed more than a dozen URL parsing libraries and showed how inconsistencies can lead to various types of vulnerabilities. Industrial organizations have been advised not to ignore these findings.
Different libraries can parse the same URL in different ways and these inconsistencies can lead to unexpected behavior that could be abused by malicious actors.
Researchers from Claroty and Snyk have analyzed 16 URL parsing libraries, including urllib, urllib3, rfc3986, httptools (all written in Python), libcurl (cURL), Wget (Chrome), Uri (.NET), URL (Java), URI (Java), parse_url (PHP), url and url-parse (NodeJS), net/url (Go), uri (Ruby) and URI (Perl).
The analysis revealed five types of inconsistencies: scheme confusion (URLs with malformed or missing scheme), slash confusion (URL with irregular number of slashes), backslash confusion (URLs containing backslashes), URL encoded data confusion (URLs containing URL encoded data), and scheme mixup (a URL belonging to a certain scheme without a scheme-specific parser).
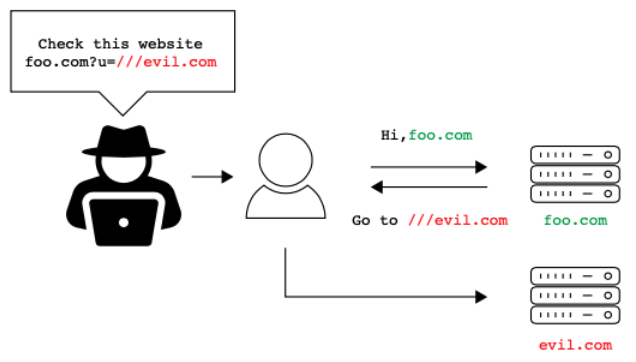
These inconsistencies could lead to five types of vulnerabilities, including server-side request forgery (SSRF), open redirect, cross-site scripting (XSS), denial of service (DoS), and filter bypass issues. In some cases, an attacker may even be able to execute arbitrary code.
Eight CVE identifiers have been assigned to the vulnerabilities found by Claroty and Snyk researchers. These security holes were privately disclosed to developers and patched before findings of the research were made public:
- Flask-security (Python, CVE-2021-23385)
- Flask-security-too (Python, CVE-2021-32618)
- Flask-User (Python, CVE-2021-23401)
- Flask-unchained (Python, CVE-2021-23393)
- Belledonne’s SIP Stack (C, CVE-2021-33056)
- Video.js (JavaScript, CVE-2021-23414)
- Nagios XI (PHP, CVE-2021-37352)
- Clearance (Ruby, CVE-2021-23435)
One specific example of a vulnerability related to URL parsing confusion is the recent Log4Shell flaw affecting the widely used Log4j logging utility.
Exploitation of Log4Shell involves sending a specially crafted request to the targeted system. The request generates a log using Log4j, which leverages the Java Naming and Directory Interface (JNDI) lookup feature to perform a request to an attacker-controlled server, from which a malicious payload is fetched and executed.
Developers initially attempted to mitigate the issue by preventing abuse of the JNDI feature through modifications inside the lookup process. However, due to the fact that two different URL parsers were used in the lookup process — one for validating the URL and another for fetching it — the mitigation was bypassed.
Implications for industrial systems
Noam Moshe, a vulnerability researcher at Claroty, has shared some information with SecurityWeek on the implications of URL parsing confusion for industrial systems.
“Due to the use of modern technologies by a large percentage of industrial and industrial adjacent platforms, URL parsing confusions are likely to increase in prevalence, resulting in more vulnerabilities involving URL parsing,” Moshe explained. “For example, modern smart sensors report data to cloud environments via web-based technologies. These technologies are utilizing URLs in many ways – from constructing a request, to parsing data. Understanding how URLs are built and handled is key to understanding the attack surface of modern OT/IoT equipment.”
“In order to mitigate the risks associated with this type of vulnerability, we recommend that developers of operational and industrial technologies read our article and implement our recommendations,” Moshe added.
Related: Severe Code Execution Vulnerabilities Affect OpenVPN-Based Applications
Related: Vulnerability Allows Remote DoS Attacks Against Apps Using Linphone SIP Stack












