Researchers at FireEye-owned security firm Mandiant have spotted more than a dozen Cisco routers on which attackers planted malicious firmware that allows them to maintain persistence in the targeted organization’s network.
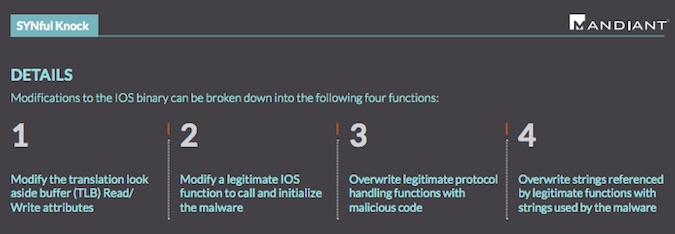
IOS, the operating system that runs on most Cisco routers and switches, uses a bootstrap program called ROM Monitor (ROMMON) to initialize the hardware and boot the software. Cisco issued an alert one month ago to warn customers that attackers had been using a legitimate ROMMON field upgrade process to install a malicious image on devices.
Mandiant says it has spotted such “implants,” which the company has dubbed “SYNful Knock,” on 14 Cisco routers located in Ukraine, Philippines, India and Mexico.
The attacks don’t involve the exploitation of a vulnerability. Instead, malicious actors can modify the firmware either by using stolen credentials, or by having physical access to the targeted router. Mandiant believes the attackers have either managed to get their hands on admin credentials, or the compromised devices had been using default credentials.
Mandiant says Cisco 1841, 2811, 3825 and likely other router models are affected. It’s worth noting that Cisco 1841, 2811 and 3825 integrated services routers are no longer being sold.
Once they modify the firmware on the targeted router, attackers have unrestricted backdoor access to the device via the console and Telnet using a special password.
The malware allows attackers to load various functional modules on the Cisco router using specially crafted TCP packets sent to the device’s interface.
“The modules can manifest themselves as independent executable code or hooks within the routers IOS that provide functionality similar to the backdoor password,” researchers explained in a blog post.
Experts have pointed out that while the implant is persistent, the 100 additional modules that can be loaded by the attackers reside in volatile memory and they are removed after a reboot or reload of the device.
Router implants such as SYNful Knock can pose a serious threat to organizations. Routers can be located both on the boundaries and in the core of a network, which gives attackers an easy entry point, allows them to maintain persistence, and enables them to gain access to other hosts, including ones that might store valuable information.
On the other hand, detecting and mitigating threats like SYNful Knock is not always an easy task and, according to FireEye, organizations often overlook routers and focus their efforts on protecting endpoints, mobile devices and servers.
“Given their role in a customer’s infrastructure, networking devices are a valuable target for threat actors and should be protected as such. We recommend that customers of all networking vendors include methods for preventing and detecting compromise in their operational procedures,” Cisco said in a blog post summarizing the steps that need to be taken to detect and mitigate such attacks.
The process outlined by Cisco has four main steps: hardening devices, instrumenting the network via telemetry-based infrastructure device integrity monitoring, establishing a baseline, and analyzing deviations from that baseline.
“We believe that the detection of SYNful Knock is just the tip of the iceberg when it comes to attacks utilizing modified router images (regardless of vendor),” FireEye said. “As attackers focus their efforts on gaining persistent access, it is likely that other undetected variants of this implant are being deployed throughout the globe.














