New Security Templates from Illumio Help Close Security Gaps Inside Data Centers and Clouds
Ensuring security policy implementation conforms to policy definition, and that the policy definition is correct for the environment is always hard. With IT estates in continual flux through expansion, mergers and acquisitions and cloud migrations, and with the skills gap getting wider, it is increasingly more difficult to lock things down completely. One solution could be automation.
Readymade and free policy template documents have long been available for download from the Internet. But they tend to be high level and still require detailed specification and implementation. “Security templates have been around for 20 years for servers,” explains Chris Weston, a CIO advisory consultant, “but the landscape is much more complex now. So the job has become more manual simply because it’s hard to find a one-size-fits-all answer.” It’s that manual element that lets errors creep in; while one-size-fits-all is getting increasingly difficult.
Platform providers have a unique opportunity. Not only can they provide detailed templates for their own platforms, they can automate the implementation of those templates within that environment. Illumio is perhaps first off the mark. Launched today, the Illumio Security Templates are described as “downloadable, tested and validated policy packs that provide all the segmentation rules needed to write a security policy for common enterprise applications or application components.”
But these are not simply written documents that require manual installation — they provide a completely automated policy implementation within the Illumio Adaptive Security Platform (ASP). They start from a baseline of the application provider’s own security recommendations, and then apply those recommendations to the installation.
“Illumio’s Security Templates let security and operations teams be as agile as they need to be,” explains Matthew Glenn, vice president of product management at Illumio. “With ‘push-button’ policies, IT no longer needs to laboriously create manual (and error-prone) segmentation rules in switches and firewalls from scratch. Our security templates take the work out of categorizing applications, or modifying the network to secure these critical applications. Applying pre-tested rule sets rapidly and accurately enables truly adaptive segmentation approaches for applications.”
Simply implementing a security policy is only half the battle — it needs to be maintained. The danger here is that experienced staff move on, inexperienced staff move in, and the environment continues to grow and contract. But provided the environment remains within the ASP, Illumio’s templates can be continuously aware of the applications and information flows between them.
When Exchange talks to Active Directory it is difficult to understand and be aware of all the different processes — and in security, what you don’t know you cannot defend. For example, Net Logon can easily use 10,000 or more dynamic ports as it communicates with Active Directory — so the port chosen and used at any given time can be unpredictable, and policy creation is complex.
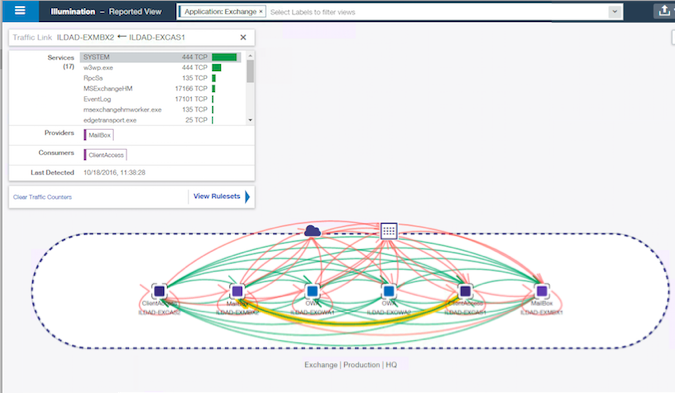
The templates integrate with Illumio’s ‘Illumination’ console graphic display. This display monitors all live application flows within ASP. Where those flows are in accordance with policy, the flows are shown as green lines; otherwise they show red.
Whenever a red line appears, the templates can be invoked and the correct policy enforced for that information flow. The red line will then return to green. The advantage of this approach is that the environment is continually monitored automatically for policy violations — and if they occur they can be rectified rapidly, easily and automatically; and be verified by Illumination.
Templates have been prepared for many of the leading data center applications, such as Active Directory Domain Communication Server 2008/2012 R2, SharePoint 2013, Exchange 2013, SQL Server 2014, Mongo DB and MySQL DB. Illumio expects to add to the list of applications over the coming months.
The downside with Illumio’s Security Templates is that they can only work for Illumio ASP customers. Nevertheless, Illumio’s chief commercial officer Alan Cohen points out that other security platform providers will undoubtedly follow.
Illumio raised $100 million Series C financing in April 2015, bringing the total raised by the company to more than $142 million in just over two years.

