Researchers at cybersecurity firm Forescout have shown how various vulnerabilities discovered in recent years in industrial control systems (ICS) can be chained for deep lateral movement in operational technology (OT) networks, and even to cause significant physical damage.
Two vulnerabilities found last year in Schneider Electric’s Modicon programmable logic controllers (PLCs) are at the center of this research. The security holes can be exploited for remote code execution (CVE-2022-45788) and authentication bypass (CVE-2022-45789), and they were addressed by the industrial giant in January.
The issues were actually discovered as part of Forescout’s OT:Icefall research, which led to the discovery of dozens of flaws across the products of several major vendors. However, Schneider had asked the security firm not to disclose these two vulnerabilities when it made the OT:Icefall research public.
The Modicon PLC vulnerabilities can be chained with known security flaws in products from other vendors for an exploit that enables deep lateral movement in an OT network.
Deep lateral movement can be useful to sophisticated attackers, as it allows them to gain access to ICS that might otherwise be difficult to reach. In addition, it can allow threat actors to gain granular control over industrial devices.
[ Read: Cyber Insights 2023 | ICS and Operational Technology ]
In order to demonstrate the impact of its research, Forescout showed how hackers could target the systems that power a movable bridge. The company said this type of attack would be very difficult to carry out by an attacker who has simple control over a supervisory control and data acquisition (SCADA) interface.
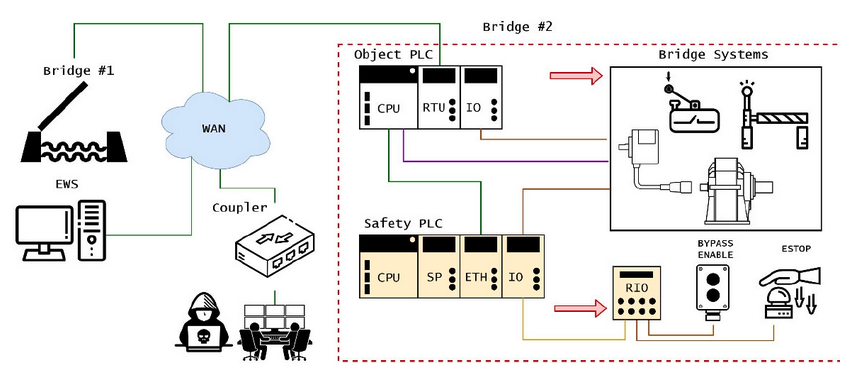
The attack scenario, described in detail in a research paper published this week, involves an attacker first exploiting a vulnerability in a Wago coupler to enable communications with a Modicon PLC. The attacker then bypasses the UMAS service authentication on the PLC and achieves remote code execution on the PLC in an effort to move to the bridge control system’s internals.
From there, the hacker can manipulate field devices connected to the controller. Before they can attempt to cause any physical damage, the threat actor also exploits a remote code execution vulnerability in an Allen Bradley safety controller that is designed to prevent accidents.
The attack method is stealthy, allowing the hacker to conduct a wide range of malicious activities without raising suspicion.

As for the real-world impact of such a hack, in the case of the bridge scenario described by Forescout, an attacker could leverage their access to tamper with the lock bar in order to cause the bridge to become blocked in a partially open position.
The attacker could also cause the bridge to close at full speed (without decelerating before it’s fully closed), or initiate a closing sequence and triggering an emergency stop when the bridge leaf is at maximum velocity. Both can cause significant damage to the structure.
Related: 2022 ICS Attacks: Fewer-Than-Expected on US Energy Sector, But Ransomware Surged
Related: Hackers Can Exploit GE Historian Vulnerabilities for ICS Espionage, Disruption

