IBM has introduced a quantum-safe roadmap to help the complex organizational transition to post-quantum cryptography at this year’s annual Think conference.
There are deadlines by which federal agencies must complete the transition to quantum-safe cryptography. Business is expected to follow the same path, but it is a long and difficult route. IBM has developed a three-stage solution it calls the IBM Quantum Safe Roadmap.
“This roadmap serves as a commitment to transparency, predictability, and confidence as we guide industries along their journey to post-quantum cryptography. There’s a lot happening at once — new algorithms, standards, best practices, and guidance from federal agencies. We hope that this roadmap will serve as a navigational tool through this complex landscape,” it announced.
The background is the assumption that much of our current cryptography will be easily cracked with the arrival of cryptographically relevant quantum computers, which are expected earlier than general-purpose quantum computers. Even though this may be several or even many years in the future, encrypted confidential data stolen by nation-state or criminal gangs now will become readable at that time. Quantum safety is a pressing concern.
NIST has been running a competition to develop new algorithms capable of withstanding decryption by quantum computers. In July 2022, it announced that it had selected four algorithms for standardization (three of which were developed with IBM involvement). These standards will be published and become official in 2024.
In November 2022, the OMB issued a Memorandum on Migrating to Post-Quantum Cryptography, including details with timelines on the steps required of federal agencies. “This memorandum describes preparatory steps for agencies to undertake as they begin their transition to PQC by conducting a prioritized inventory of cryptographic systems,” it announced.
The IBM Quantum Safe Roadmap is designed to help both federal agencies and business enterprises meet both the requirements and the deadlines for quantum safe cryptography.
The roadmap comprises three separate products – two of which are available now, with the third currently in its first generation but timed to be fully available at the time it is needed. The three products are Quantum Safe Explorer, Quantum Safe Advisor, and Quantum Safe Remediator. These three products correspond to the discover, observe, and transform stages of the roadmap.
The Explorer enables organizations to scan source and object code to locate cryptographic assets, dependencies, and vulnerabilities. The result is what IBM calls a cryptography bill of materials (CBOM), aggregating all relevant details into a single location.
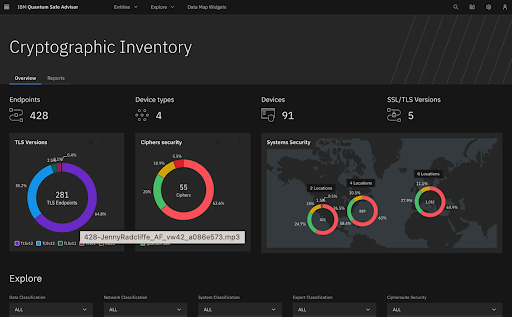
The Advisor creates a dynamic view of the cryptographic inventory to guide remediation, and analyzes cryptographic posture and compliance to prioritize risks.
The Remediator enables organizations to deploy and test best practice-based quantum-safe remediation patterns to understand the potential impacts on systems and assets as they prepare to deploy quantum-safe solutions. “It allows you to work with different quantum-safe algorithms, certificates and key management services,” says IBM. “It also helps you achieve crypto agility so that you can quickly adapt to changing policies and threats without significant operational or budgetary implications.”
In 2025, the NSA will require national security systems to prefer quantum-safe algorithms while configuring their systems. Use of such algorithms will become mandatory for commercial products used in these systems, meaning that within two years, organizations working with the federal government will need to begin their quantum-safe transition. “By then,” says IBM, “Remediator will offer a hybrid approach, enabling traditional as well quantum-safe cryptography.”
The complexity of transitioning to quantum-safe cryptography within prescribed timelines means the urgency is already here.
“As the era of quantum computing quickly approaches reality, it is imperative that quantum-safe technologies are also deployed to protect today’s classical systems and data,” comments Patrick Moorhead, CEO and founder of Moor Insights and Strategy. “What the world needs to secure data for the quantum age is expertise in world-class quantum technology and advanced cryptography, alongside decades of product development experience for critical infrastructure. These pillars are where I believe IBM excels, and now with a quantum-safe roadmap to lead the industry and new technologies to simplify migration, I look forward to seeing the advancement of quantum-safe journeys globally.”
Related: Cyber Insights 2023 | Quantum Computing and the Coming Cryptopocalypse
Related: CISA Urges Critical Infrastructure to Prepare for Post-Quantum Cryptography
Related: NIST Post-Quantum Algorithm Finalist Cracked Using a Classical PC
Related: US Gov Issues Security Memo on Quantum Computing Risk