Hunters.AI, an Israel-based company specializing in autonomous threat hunting, on Wednesday emerged from stealth mode and announced that it raised $5.4 million in seed funding from YL Ventures and Blumberg Capital.
Founded in 2018, Hunters is led by Uri May (CEO) and Tomer Kazaz (CTO). The company was also co-founded and incubated by Chairman Ehud Schneorson, Yodfat Harel Buchris and Idan Nurick.
Hunters’ autonomous solution, expected to become generally available in late 2019, is designed to help security and security operations center (SOC) teams identify threats by continuously collecting data from existing management, visibility, monitoring and security tools. The technology can analyze and correlate raw data in an effort to pinpoint attacks.
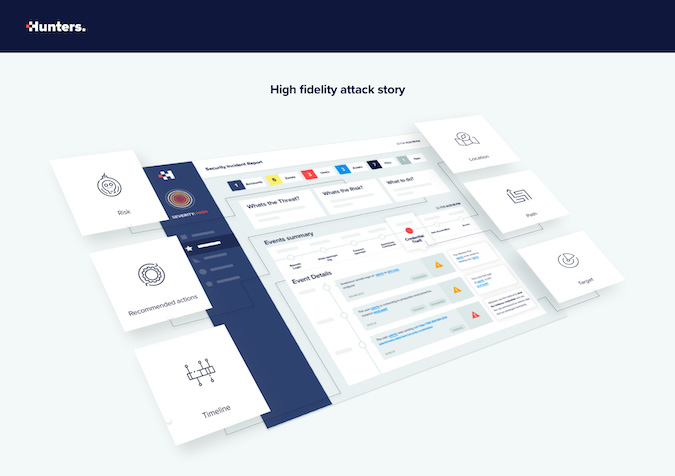
The company says its solution can also expose hidden breaches and security risks and provide a contextual attack story, including a timeline, locations, paths, targets and potential impact.
The Hunters platform is completely cloud-based and it should be easy to deploy, without requiring the installation of agents on protected endpoints, which the company claims sets it apart from competitors such as CrowdStrike and Carbon Black.
Snowflake Computing, an early Hunters customer, used the threat hunting platform during a recent Red Team exercise. The attack scenario involved an attacker who had credentials to an admin account and a laptop belonging to the targeted company.
“The result was amazing,” said Mario Duarte, VP of security at Snowflake Computing. “Hunters identified the attack in minutes, alerted our team and they resolved it. While that might sound easy, it is not. If an attacker has credentials and access to a compromised company device, traditional monitoring systems cannot tell the difference from a legitimate employee and an attacker. But Hunters autonomous hunting technology did find it. In my 20 years in security, I have not seen anything as effective, fast and with high fidelity as what Hunters can do.”
Related: Threat Hunting Tips to Improve Security Operations
Related: Amazon Acquires Threat Hunting Firm Sqrrl
Related: Profile of a Threat Hunter

