Hackers’ Investment in Evasion Techniques Proves That They See Web Applications as a Valuable Attack Surface
Network security devices, such as network antivirus (AV) solutions or web application firewalls, protect computer systems by stopping malicious traffic before it even reaches them. In order to assess whether the examined traffic is malicious or benign, the security device typically needs to mimic the processing done on the protected system. If the security device interprets the traffic in a different way than the protected system, a semantic gap is created. The attackers can use that semantic gap, in order to create traffic that will bypass the security device, and still create a malicious effect on the protected system. The exploitation of a semantic gap is often called an “evasion technique”.
 For example, a common rule in network antivirus solutions is to block the transfer of executable files. A naïve antivirus implementation might assess whether a file is an executable based solely on the file extension, while modern operating systems ignore the extension and rely on file headers, by thus creating a semantic gap. The attacker can exploit the semantic gap and with the following “evasion technique”: simply renaming the executable file extension from “.exe” to “.txt”
For example, a common rule in network antivirus solutions is to block the transfer of executable files. A naïve antivirus implementation might assess whether a file is an executable based solely on the file extension, while modern operating systems ignore the extension and rely on file headers, by thus creating a semantic gap. The attacker can exploit the semantic gap and with the following “evasion technique”: simply renaming the executable file extension from “.exe” to “.txt”
I would like to show why evasion techniques are actually a good thing, as they provide validation for the security market and allow able network security devices to increase the security of the protected systems.
Mind the semantic gap
Earlier this year, researchers from the University of Texas, published an excellent paper on network antivirus evasion. They give a few reasons why it is very difficult to write a “perfect” processor that precisely replicates the processing semantics of the defended system:
• Protocols are often underspecified: Not all corner cases are covered by the protocol specification. For others, the description exists, but may be lacking or vague.
• Formats and protocols are usually complex: Replicating the behavior of a given processor is hard—for example, after many years of testing, there are still hundreds of file-parsing discrepancies between OpenOffice and MS Office.
• Lax implementation of the protocol in the application – In order to handle even malformed messages, application processing algorithms are much looser than the format specification.
Each time two (or more) vendors implement the processing of a certain element in a different way, a virtual junction is created. The network security device has to choose a processing path in that junction. The road not taken usually represents an evasion technique.
Evasion is the hackers’ sincerest form of flattery
Over the years, a lot of research has been conducted on semantic gaps on the web application arena. Web Application Firewalls (WAFs) evasion techniques has been published based on semantic gaps in application and web servers. Moreover, the hacker’s community is actually using evasion techniques, as SQL injection tools such as Havij and SQLmap contain some explicit anti-WAF evasions.
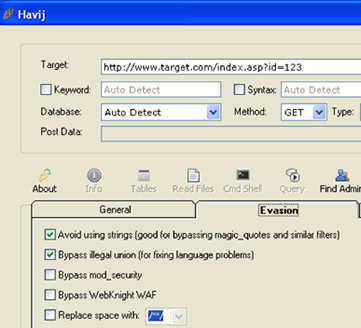
Figure 1 – Havij’s WAF evasion configuration screen
Hackers’ investment in evasion techniques proves that hackers view web applications as valuable attack surface and that WAFs are threat for them, otherwise they would not bother with eluding them.
Planting mines on the road not taken
We had seen that an evasion technique creates a junction and the WAF must follow the appropriate trail, the same trail the defended application takes.
How would a good WAF know the right trail?
• Choose the correct path with flexible parsing – allow WAF parsing to be configured according to the specifics of the defended servers. Thus providing support for specific implementation anomalies and bugs.
• Don’t go into dark alleys and avoid unnecessary junctions by using:
o Protocol hardening – Detect deviations from the protocol to defend against evasion techniques that abuse lax protocol implementation on the server side.
o Positive security model hardening – Learn the usual operation of the web application to detect deviations from the application usual operation. Evasion techniques that abuse corner cases on the server side HTTP implementation will probably deviate from application’s normal.
A surprising yet very nice corollary of the last argument is the ability to plant mines on the road not taken. The WAF can detect an attack by the detecting the mere use of evasion technique.
By using evasion techniques hackers break the most basic principle of hiding as stated by Sherlock Holmes: “the best place to hide something, is where everyone can see it”. The evasion technique usage just draws more attention from the WAF and actually helps the WAF to block the attack.
Related Reading: Web Application Firewalls: Three Benefits You May Not have Considered
Related Reading: Evaluating Network Firewalls – Are you Armed?












