IT management software maker Kaseya on Monday said the recent ransomware attack impacted up to 1,500 organizations, but claimed there was no evidence of malicious modifications to product source code.
Kaseya on Friday urged customers to immediately shut down on-premises servers running its VSA endpoint management and network monitoring tool due to a cyberattack, which, it later turned out, exploited a zero-day vulnerability in the product.
The company has provided regular updates regarding the incident. While it initially said that less than 40 of its 36,000 customers were impacted, by Monday the number increased to “fewer than 60.”
The number of impacted Kaseya customers is relatively small, but the company’s products are used by managed service providers (MSPs) and the attackers were able to deliver the ransomware to the customers of those MSPs as well. Kaseya estimated that the attack impacted “fewer than 1,500 downstream businesses.”
Cybersecurity firm Kaspersky, which has also monitored the attack, said its products detected more than 5,000 attack attempts across 22 countries.
Swedish grocery chain Coop, whose PoS supplier uses an MSP hit by the Kaseya attack, was forced to close down a majority of its 800 stores.
Kaseya said the incident only impacted its VSA product, and only on-premises customers, but it has also shut down its SaaS servers as a precaution. The company hopes to restore SaaS servers on Tuesday.
As for the zero-day vulnerability exploited in the attack, the hackers appear to have leveraged an authentication bypass flaw affecting the VSA web interface to upload a malicious payload. They were then able to execute arbitrary code on compromised systems.
The Dutch Institute for Vulnerability Disclosure (DIVD) reported that its researchers had independently discovered some of the vulnerabilities exploited in the Kaseya attacks as part of a research project and informed the vendor. DIVD, which mentioned the CVE identifier CVE-2021-30116, said Kaseya had been in the process of patching the vulnerabilities, but the cybercriminals launched the attack before the fixes were completed.
DIVD reported on Sunday that the number of internet-exposed instances of VSA dropped from more than 2,200 to less than 140 since the incident came to light.
In its latest update, Kaseya said the patch is going through the testing and validation process, and it expects it to become available within 24 hours after SaaS servers have been restored.
The company pointed out that the attackers abused legitimate VSA functionality to deliver the ransomware to endpoints, and there is no evidence that they made malicious changes to the VSA source code.
Kaseya has also made available a compromise detection tool, which had been downloaded by more than 2,000 customers as of Monday.
The attack was conducted by a threat group that uses the REvil/Sodinokibi ransomware. While REvil operators typically also steal data in an effort to increase their chances of getting paid, in this case it appears they only managed to encrypt files on compromised systems.
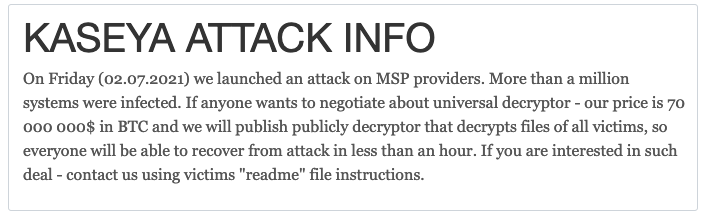
The cybercriminals claimed their malware infected more than a million systems. Each victim has been instructed to pay a certain amount of money to recover files — the amounts reportedly range between tens of thousands and millions of dollars. However, they said they are willing to provide a “universal decryptor” that can be used to recover the files of all victims for $70 million in bitcoin.
Security researcher Jack Cable later reported that the hackers had lowered the price to $50 million for the universal decryptor and were also offering decryptors that work only for certain file extensions. They claim prices for these individual decryptors are negotiable.
Technical information on the attack has been provided by Kaseya, as well as by several cybersecurity companies, including ESET, Huntress, Sophos and Kaspersky. CISA and the FBI also offer guidance for the MSPs and their customers hit by this supply chain attack.

