Google this week announced improved malware protection capabilities for all users who are enrolled in its Advanced Protection Program.
Aimed at providing high-risk users such as politicians and their staff, business executives, journalists, and activists with an additional layer of protection for their accounts, the Advanced Protection Program was launched in October 2017. Any user can enroll to take advantage of the improved security options.
Initially, the program required the use of physical security keys, but Google started including security keys in Android phones last year, and announced support for activating security keys on iPhones earlier this year.
Following new additions to the Advanced Protection Program that were announced in early summer, Google this week announced that it decided to improve the malware protections available for the users who signed up for the program.
Thus, the first step the Internet search giant has taken is to expand Chrome’s download scanning options for these users, to complement the already available anti-phishing protections.
“Advanced Protection users are already well-protected from phishing. As a result, we’ve seen that attackers target these users through other means, such as leading them to download malware,” Google explains.
Now, in addition to displaying a warning when a downloaded file may be malicious, Chrome allows Advanced Protection users to send risky files to Google’s servers, to be scanned by the more advanced malware detection technology in Safe Browsing. This should improve the detection of malicious files, the company says.
“When a user downloads a file, Safe Browsing will perform a quick check using metadata, such as hashes of the file, to evaluate whether it appears potentially suspicious. For any downloads that Safe Browsing deems risky, but not clearly unsafe, the user will be presented with a warning and the ability to send the file to be scanned,” the search giant notes.
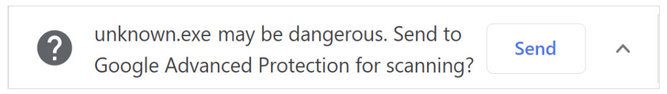
When the user sends a file, the browser uploads it to Google Safe Browsing and, if the file is deemed unsafe, the user receives a warning. However, users will be provided with the option to bypass the warning and open the file, even without scanning it, when they are confident the file is safe.
“Safe Browsing deletes uploaded files a short time after scanning,” Google also notes.
Related: Google Announces New Additions to Advanced Protection Program
Related: Google Simplifies Enrollment Process for Advanced Protection Program
Related: Many High-Risk Users Have Bad Security Habits: Google Survey












