Google’s Threat Analysis Group (TAG) this week shared some data on government-backed hacking and disinformation attempts targteting its customers.
Google has been alerting users of state-sponsored hacking attempts for several years and it has sent out thousands of warnings every month.
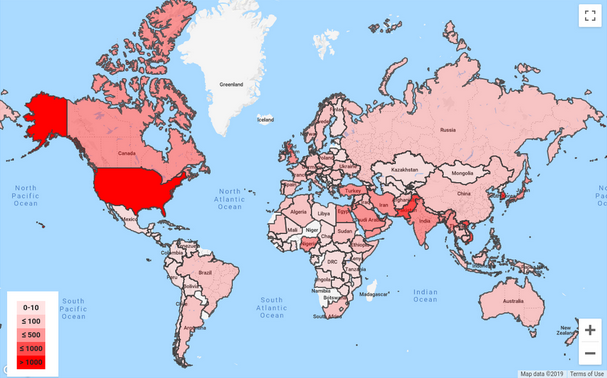
In a blog post published on Tuesday, Shane Huntley of Google TAG revealed that more than 12,000 warnings triggered by state-sponsored phishing attempts were sent out to users across 149 countries in the third quarter of 2019. The company says the number of warnings has remained roughly the same as it was in the same period of 2017 and 2018.
The United States was the number one target of these types of attempts in the third quarter of 2019, followed by Pakistan.
Over 90 percent of these attacks involved attempts to convince users to hand over their account credentials, including two-factor authentication codes, which would allow the attacker to take control of the targeted account.
Google provides a service named Advanced Protection Program (APP), which high-risk users such as journalists and rights activists can leverage to better protect their accounts through the use of hardware security keys.
Google’s TAG has been monitoring the activities of over 270 threat groups that have launched targeted attacks or government-backed campaigns. Their operations have been aimed at entities in more than 50 countries, and their goal was mainly to gather intelligence, steal intellectual property, launch destructive attacks, track activists and dissidents, or spread false information.
One of these groups is the Russia-linked Sandworm, which in the past years uploaded or attempted to upload several malicious Android apps to the Google Play Store. Some of these applications targeted users in South Korea and Ukraine.
As for the disinformation campaigns it has targeted recently, Google mentioned a Russia-linked influence operation aimed at several countries in Africa, and a campaign targeting Indonesia’s Papua and West Papua provinces.
Related: Google Took Down 2.3 Billion Bad Ads in 2018
Related: Google Warns Users of Recent State-sponsored Attacks
Related: Google Offers G Suite Alerts for State-Sponsored Attacks













