Important Google services were inaccessible for some users on Monday due to a BGP leak that caused traffic to be directed through Russia, China and Nigeria. It’s unclear if the incident was caused by a configuration issue or if it was the result of a malicious attack.
The Border Gateway Protocol (BGP) controls the route of data across the Internet. BGP hijacking (route hijacking) and BGP leaks occur when IP address groups are intentionally or accidentally taken over by corrupting the routing tables that store the path to a network.
According to network monitoring company ThousandEyes, a BGP leak occurred on Monday when traffic to Google Search, G Suite and various Google Cloud services was directed through TransTelecom in Russia, Nigerian ISP MainOne, and China Telecom, where the traffic was getting dropped.
BGPmon, which monitors BGP routing information in real-time, reported that 212 unique Google prefixes were impacted. The incident mainly affected business-grade service providers rather than consumer ISPs, ThousandEyes noted.
“This incident at a minimum caused a massive denial of service to G Suite and Google Search. However, this also put valuable Google traffic in the hands of ISPs in countries with a long history of Internet surveillance,” ThousandEyes said in a blog post.
The company said it was unclear if this was a malicious attack or the result of a misconfiguration at the Nigerian ISP, but highlighted that the incident demonstrates no one is immune from BGP hijacks and leaks.
“Our analysis indicates that the origin of this leak was the BGP peering relationship between MainOne, the Nigerian provider, and China Telecom. MainOne has a peering relationship with Google via IXPN in Lagos and has direct routes to Google, which leaked into China Telecom,” ThousandEyes explained.
The firm reported seeing a suspicious announcement for a Google IP address at 12:45 PST, and Google claimed to have resolved the issue by 14:35 PST.
“Throughout the duration of this issue Google services were operating as expected and we believe the root cause of the issue was external to Google. We will conduct an internal investigation of this issue and make appropriate improvements to our systems to help prevent or minimize future recurrence,” Google told users on its Cloud Platform status page.
Researchers claimed recently that China Telecom has been constantly hijacking traffic over the past years, including from the United States, and directing it through China.
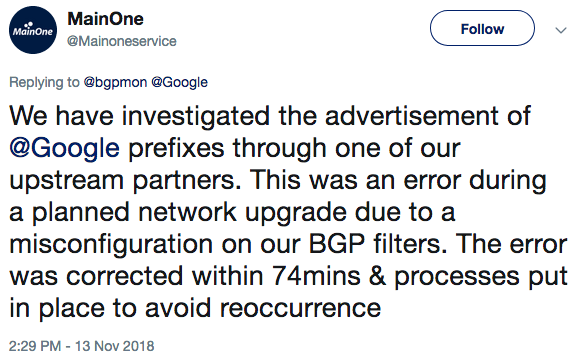
UPDATE. Nigeria’s MainOne has confirmed that the BGP leak was caused by a misconfiguration.
Related: BGP Hijacking Attacks Target US Payment Processors
Related: Embrace RPKI to Secure BGP Routing, Cloudflare Says












